This time it was a Certificate Authority (again). Not just any CA, either, but an official CA that manages the “PKIOverheid” for the government of the Netherlands. In other words, a really important CA, even in a league where most, if not all, CA’s are important.
This time it was a Certificate Authority (again). Not just any CA, either, but an official CA that manages the “PKIOverheid” for the government of the Netherlands. In other words, a really important CA, even in a league where most, if not all, CA’s are important.
What happened? They got breached. They got breached in a way that allowed attackers to create at least 531 rogue certificates with their trust models. How did they get breached? It seems to stem from a combination of attackers exploiting basic issues to gain access, then leveraging more advanced custom skills to get the certificates generated and extrude them. I am basing that opinion on the Fox-IT report located here. (The report itself is well worth a read).
The critical issues identified?
- Lack of a secure architecture for CA servers (1 Windows domain, connectivity from management network)
- Missing patches
- Lack of basic controls (AV, in this case) which allowed exploitation by basic attacker tools such as Cain/Abel
- Poor password policies, logging and management of detective controls
If you follow our blog, attend our talks or listen to our podcasts, you should be seeing this as another reminder of just how critical it is to do the basics. Having powerful tools that no one watches, engaging vendors to do assessments that you ignore and spending money on controls that don’t matter won’t create an effective information security program. Getting the basic controls and processes in place might not protect you from breaches against resourced, skilled attackers completely, either, but it will go a long way toward giving you some protection from the most common threat models. In this case, it might have helped a CA know when they were under attack and take action against their threat sources to mitigate the breach before they got to the crown jewels or in this case, the crown certificates.
The attacker has been posting to Pastebin, (presumably the attacker), that they have access to other CA providers. If you are a CA or run a certificate system, now might be a good time to have someone take an independent third-party look around. It might be a good time to spend a few extra cycles on “just checking things out”.
If your organization is still stuck chasing vulnerabilities and hasn’t done a holistic review of their overall program, this would be a good impetus to do so. It should become an action item to look at your program through the lens of something like the SANS CAG or our 80/20 of Information Security lens and ensure that you have the basics covered in an effective manner. If you have questions or want to discuss the impacts or issues some of these recent breaches have against your organization, give us a call. As aways, thanks for reading and stay safe out there.
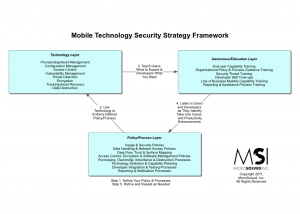
 Wondering how Apple’s iOS5 and the iCloud will affect your life? Check our recent slide deck that tackles some potential challenges as Apple gets ready to roll out their newest creation. In this deck, you’ll learn:
Wondering how Apple’s iOS5 and the iCloud will affect your life? Check our recent slide deck that tackles some potential challenges as Apple gets ready to roll out their newest creation. In this deck, you’ll learn: