Positive Train Control: Skating away on the thin ice of a new day?
From the movie “The Polar Express“
That line: “Skating away on the thin ice of a new day” is from a Jethro Tull song by the same name. (Yes – I am that old 😉 ).
It came to me as I was reflecting on the reading I’ve been doing on the topic of “Positive Train Control“ (PTC).
PTC is an idea rather than any specific technology or architecture.
Its intent is to minimize the chance that railroad operator error (e.g. missed communication) can lead to loss of life or a major train-to-train collision. It’s “positive” in that a positive action (e.g. stop the train) is automatically done if an operator does not respond appropriately.
Think a pinball machine with a “smart” controllable pinball.
In the US it is mandated for a large subset of railroads by the Rail Safety Improvement Act of 2008. The current target date is December 31, 2018, moved from the original date of December 31, 2015 when it became clear that a number of railroads would not be able to make the original date. Even now there are provisions for moving the target to December 2020 for those railroads that have shown real progress in implementation. Financial penalties for non-compliance eventually kick in.
Several highly-publicized rail accidents were the motivation for the law, notably the 2008 Chatsworth collision in which a commuter and freight train collided, causing 25 deaths. The commuter train engineer missed a stop signal. He had worked a split shift, was likely fatigued, and was using a cell phone to text repeatedly prior to the collision.
So – all good, right? Government acting responsively to protect citizens?
Well… yes. But…
PTC is not a prescribed architecture. It’s a desired outcome. Industry groups, often dominated by the big Class 1 freight railroads, are adopting various technologies to accomplish the goal. Interoperability between railroads is an issue, with some railroads having to install 2 or more PTC solutions on their infrastructure to accommodate the different PTC environments that may be encountered on the various track they run on.
PTC also introduces a dependency on software and network communication in an arena in which local human control was traditionally paramount.
And there’s the issue for me.
Given the urgency of the federal mandate and the associated hurried activity, the apparent lack of defined software security standards, and the historic preference for availability over information security that understandably pervades ICS environments, it’s seems very likely that the solutions being implemented will have exploitable software flaws.
Europe has been down this path much longer than the US – and the problem appears to be very real there, as revealed by the SCADA Strangelove researchers in a “sanitized” presentation on the security of European train control systems a few years ago.
Note: These same researchers published a collection of default logins that are found hardcoded in some of the equipment used by PTC equipment vendors here in the US.
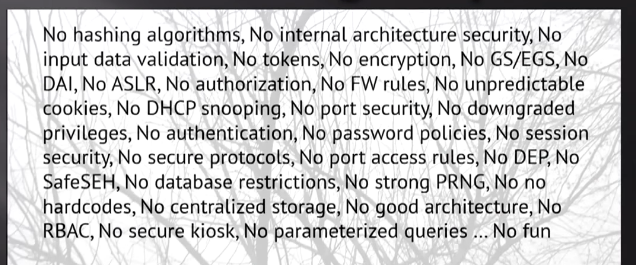
In their presentation, this slide appears as part of the discussion of what was found when analyzing European train control software. .
Not a pretty picture.
My take is that “nation-state” attackers will be going after the suppliers of the tech intended to be used for PTC in the US. Going after an industry target by way of its vendors, some of whom can always be relied on to have inadequate cyber-defenses, has a well established history.
Just ask Target.
Suppliers to the railroad industry, particularly those supplying tech for PTC, will have to start seeing themselves as just that sort of “target” and ensure that their own information infrastructure is secure, monitored, and – most importantly – that their employees are trained to detect and report the inevitable phishing attacks that have become the fast path to compromise.
PTC, on the surface, appears to be an inarguably good idea and has achieved considerable momentum in the US.
But without coordinated consideration of the new cyber attack surfaces that may be opened to America’s enemies, that momentum could well put a critical part of US infrastructure out on to a new, and very dangerous, patch of “thin ice”.
See:
- US Railroad classifications: https://en.wikipedia.org/wiki/Railroad_classes
- Industry testing facility: http://www.ttci.aar.com/
- Association of American Railroads: https://www.aar.org/article/freight-rail-positive-train-control/
- Wabtec’s “Interoperable” Electronic Train Management System: https://www.wabtec.com/products/1454/i-etms%E2%84%A2
- Railroad industry objections to mandated cybersecurity: Quote: “The Association of American Railroads (AAR) is among 46 business and trade organizations that have asked congressional leaders to remove a Senate cybersecurity bill provision that would allow the Department of Homeland Security (DHS) to regulate the cyber practices of “critical infrastructure” entities. https://progressiverailroading.com/federal_legislation_regulation/news.aspx?id=46467
- Dual PTC solutions: http://trn.trains.com/railroads/abcs-of-railroading/2018/02/what-is-positive-train-control Quote: “Rather than installing multiple systems in locomotives… NS is looking to “dual-equip” wayside units along the Northeast Corridor where NS freight and Amtrak passenger trains share the right-of-way for short stretches“
- SCADA Strangelove presentation:
- https://youtu.be/IWAoAq6sz8w – full video
- https://securityaffairs.co/wordpress/43344/hacking/experts-disclosed-scadapass.html
- https://www.securityweek.com/trains-vulnerable-hacker-attacks-researchers
- Eventual government oversight of rail cybersecurity?: https://www.dhs.gov/news/2018/08/13/vice-president-pence-time-has-come-cybersecurity-and-infrastructure-security-agency
If you would like to know more about MicroSolved or its services please send an e-mail to info@microsolved.com or visit microsolved.com.
Videos:
https://www.aar.org/article/freight-rail-positive-train-control/