 After I published the blog posts about the sample IT maps a few weeks back, questions started to come in about how those maps could be created for ICS/SCADA deployments.
After I published the blog posts about the sample IT maps a few weeks back, questions started to come in about how those maps could be created for ICS/SCADA deployments.
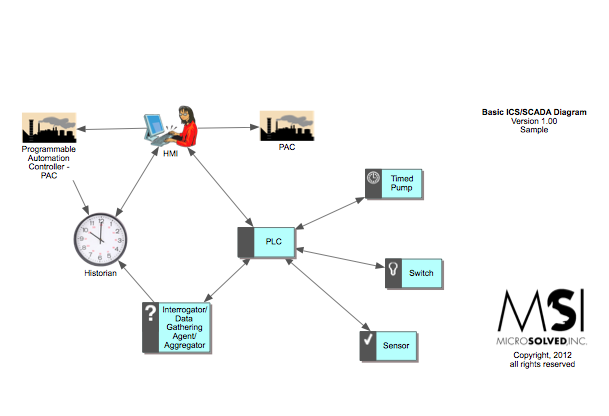
I thought I would take a few minutes and create quick sample maps for folks to visualize what that might look like. In this case, I built a set of compound maps that show first, the basics of the process. Then I added data flow, trust mechanisms and eventually attack surfaces with the smallest bit of vulnerability insight thrown in. Click the links below to download the PDFs:
The goal would be to create a set of maps like this for each process or deployment, eventually leading to a master map that showed high level relationships between your deployments.
Imagine how helpful these maps would be in an assessment or audit. Being able to show an auditor a strong set of diagrams of your controls and what your team knows about your environment is a powerful thing. Imagine the usefulness of this data in an incident. You could quickly, easily and effectively estimate the width and depth of compromise, understand what is potentially in play and even get a rough idea of what and where to look for evidence.
It might not be easy, since there is a lot of up front work to building these maps. But, every time we work through the project of creating them with clients, they learn a lot they didn’t know about their environment and their teams emerge stronger than before.
That said, give it a shot. If you want assistance or someone to do the heavy lifting, give us a call. If you want to discuss the process, reach out to me on Twitter (@lbhuston). I love to talk about this stuff, so I’m happy to help you.
As always, thanks for reading, and stay safe out there!

Sample ICS/SCADA Maps – MSI :: State of SecurityMSI :: State of Security – http://t.co/GG6GZCt7
RT @switch_d: Sample ICS/SCADA Maps – MSI :: State of SecurityMSI :: State of Security – http://t.co/GG6GZCt7
RT @switch_d: Sample ICS/SCADA Maps – MSI :: State of SecurityMSI :: State of Security – http://t.co/cSmudyhD < XD #ICS #SCADA cc @fisteuees
RT @badboy_nt: RT @switch_d: Sample ICS/SCADA Maps – MSI :: State of SecurityMSI :: State of Security – http://t.co/cSmudyhD < XD #ICS #SCADA cc @fisteuees