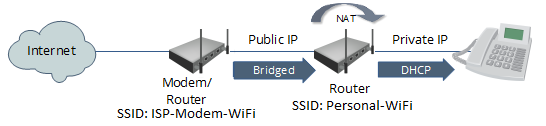
As with many home networks, you may have an all-in-one cable modem/router/wireless access point provided by the ISP, as well as your own personal router/wireless access point. To prevent a double NAT issue, the ISP router is bridged and the personal router is performing NAT and firewall functions. This setup for a friend’s home network is diagrammed as below:
All wireless devices connect to the Personal-WIFi SSID, with the wireless key saved for automatic reconnection to this access point, and behind the router’s firewall. The ISP-Modem-WiFi SSID was not disabled for the occasional connectivity and bandwidth test. However, whenever he switches to the ISP-Modem-WiFi SSID, he manually enters the wireless key and none of his wireless devices has this wireless key saved. Or so he thought.
About a month ago, he had set his laptop down close to the ISP’s modem in the basement. The laptop was on but was not being used. Later that day, he got on the laptop and noticed he couldn’t connect to any internal sources in his home network but there was internet connectivity. He moved the laptop to the den, and was then able to connect to his media server and file shares. He didn’t think anything of it.
The next day, he discovered for several hours in the previous day, the laptop had had many connection attempts from the internet, several over ftp, telnet, mssql ports. This was alarming because the attempts were coming from the public internet – how were these attempts going through the firewall?
On the laptop runs a HoneyPoint agent – MicroSolved’s proprietary honey pot application – that listens for and responds to connection attempts to specific ports. The agent will then send an alert to the HoneyPoint console for report, alerts or analyses. The laptop HoneyPoint agent had detected these connection attempts. No real service connections were established; no actual breaches occurred. The HoneyPoint agent records the source IP, port being probed, and what data was sent. The attacks indicated discovery probing with a vector towards IoT devices.
But the lingering question was, how could the connection attempts go past the firewall?
It was only serendipitous that he stumbled on the answer. About a week ago, he couldn’t RDP to a Windows box in his internal network, but still had internet. Turns out, the home wifi (Personal-WIFi SSID) was having a hiccup but the laptop had automatically switched to the ISP-Modem-WiFi SSID – outside the firewall. He had inadvertently saved the wireless key to this SSID and was not aware of it. The laptop was now bridged and getting an IP from the ISP, with no firewall or router in between. Also, almost immediately, he noticed the HoneyPoint alerts – connection attempts on the same ftp, telnet, mssql ports were coming in from the public internet.
Lesson learned = if you’re going to keep your wireless access point enabled without a firewall – as in the bridged ISP modem/router – then DO NOT save the wireless key for it on any of your devices (either intentionally or accidentally) or you may be connecting to it without being aware. Best is to disable the wireless, but if you need it, set a strong WPA2 password and do not save the key on any device.
Another lesson learned = In the ensuing troubleshoots, he discovered the router’s uPnP setting had been left enabled, its default setting. That was immediately disabled. Additionally, HoneyPoint agent is a light-on-resources, quick-alerting IDS that does its intended job.
Note of explanation: One could argue the point to bridge the personal router instead of the ISP modem/router, and you would not have this issue. However, if you have many DHCP reservations in your internal network and have ever changed ISP’s, you understand the pain of re-entering those client reservations on a new modem/router. With this setup, you can easily switch ISP’s, slide in a new modem/router and bridge it, and all internal network resources are not interrupted.
Resources: Is UPnP a Security Risk?; Disable This Buggy Feature…