One of the biggest signs that an organization’s information security program is immature is when they have an obsessive focus on prevention and they equate it specifically with security.
The big signs of this issue are knee-jerk reactions to vulnerabilities, a never-ending set of emergency patching situations and continual fire-fighting mode of reactions to “incidents”. The security team (or usually the IT team) is overworked, under-communicates, is highly stressed, and lacks both resources and tools to adequately mature the process. Rarely does the security folks actually LIKE this environment, since it feeds their inner super hero complex.
However, time and time again, organizations that balance prevention efforts with rational detection and practiced, effective response programs perform better against today’s threats. Evidence from vendor reports like Verizon DBIR/Ponemon, law enforcement data, DHS studies, etc. have all supported that balanced program work much better. The current state of the threat easily demonstrates that you can’t prevent everything. Accidents and incidents do happen.
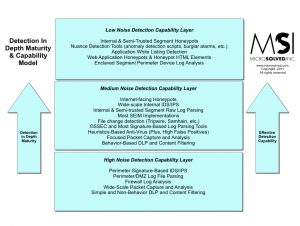
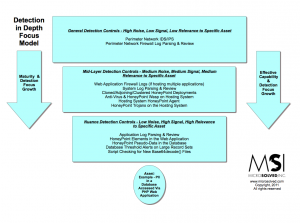
When bad things do come knocking, no matter how much you have patched and scanned, it’s the preparation you have done that matters. It’s whether or not you have additional controls like enclaving in place. Do you have visibility at various layers for
detection in depth? Does your team know how to investigate, isolate and mitigate the threats? Will they do so in a timely manner that reduces the impact of the attacker or will they panic, knee-jerk their way through the process, often stumbling and leaving behind footholds of the attacker?
How you perform in the future is largely up to you and your team. Raise your vision, embrace a balanced approach to security and step back from fighting fires. It’s a much nicer view from here.