There’s a moment in almost every security program where someone asks a deceptively simple question:
“Is 15 minutes a standard account lockout duration?”
The short answer? No.
The more honest answer? It’s common—but often wrong for the environment it’s deployed in.
And I’ve seen more than a few organizations learn that the hard way.

The Myth of the “Standard” Lockout
If you go looking for authoritative guidance—from Center for Internet Security, FFIEC, or CISA—you’ll notice something interesting:
They don’t tell you what number to use.
Instead, they consistently emphasize:
- Risk-based decision making
- Balancing usability and security
- Detecting and responding to threats—not just blocking them
That’s not an accident. It’s an acknowledgment that static controls like lockouts are blunt instruments in a very dynamic threat landscape.
What We Actually See in the Real World
Across environments—financial services, healthcare, SaaS, manufacturing—the patterns are pretty consistent:
| Setting |
Typical Range |
| Failed attempts before lockout |
3–10 |
| Lockout duration |
5–30 minutes |
| Most common default |
10–15 minutes |
So yes, 15 minutes sits comfortably in the middle.
But “common” and “effective” are not the same thing.
Where 15 Minutes Breaks Down
1. It Punishes Users More Than Attackers
A 15-minute lockout sounds reasonable—until you multiply it.
- A clinician locked out mid-shift
- A call center agent missing SLAs
- A trader unable to access systems during market hours
Now multiply that by repeated lockouts from cached credentials, mobile devices, or service accounts.
You don’t just have a security control—you have an operational problem.
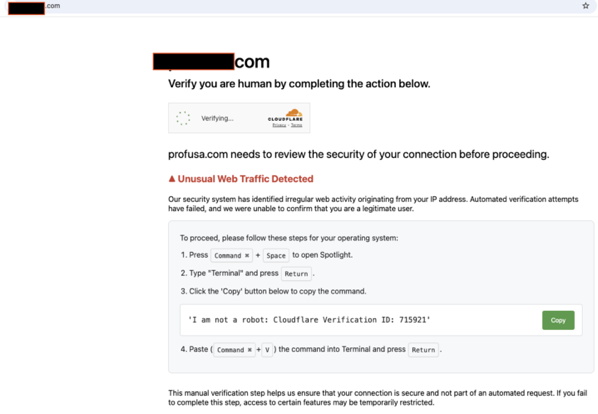
2. It Doesn’t Stop Modern Attacks
Attackers have evolved. Most environments haven’t.
Today’s common attack patterns:
- Password spraying (low-and-slow, avoids thresholds)
- Credential stuffing (valid credentials, no lockout triggered)
A longer lockout duration doesn’t meaningfully impact either.
If anything, it gives a false sense of security while the real attack path goes untouched.
What Actually Works: A Layered Approach
This is where the conversation needs to shift—from “what’s the right number?” to “what’s the right strategy?”
1. Lockouts Are Supporting Controls—Not Primary Defenses
If you’re relying on lockouts as your main protection, you’re already behind.
At a minimum, you should be pairing with:
- MFA everywhere it’s technically feasible
- Conditional access (device, location, behavior)
- Authentication throttling and smart detection
2. Tune for Risk, Not Defaults
A more balanced configuration tends to look like:
- 5–10 failed attempts
- 5–10 minute lockout
- Reset counter after a defined cooldown window
This reduces user friction while still slowing down brute-force attempts.
More importantly—it acknowledges that lockouts are a speed bump, not a wall.
3. Progressive Delays Beat Hard Lockouts
One of the most underutilized strategies is progressive delay:
- Attempts 1–2 → no delay
- Attempts 3–5 → 30–60 second delay
- Continued attempts → increasing delay
This approach:
- Degrades attacker efficiency
- Preserves user productivity
- Avoids helpdesk spikes
It’s a far more surgical control than a blanket 15-minute lockout.
4. Detection Over Punishment
Modern security programs don’t just block—they observe.
You should be:
- Logging all failed authentication attempts
- Alerting on patterns (spraying, geographic anomalies)
- Correlating identity signals across systems
Lockouts should be one signal among many—not the primary response.
Implementing This in Active Directory
Let’s get practical.
In on-prem Active Directory, you’re working primarily with Group Policy.
Recommended Baseline
In your domain or fine-grained password policy:
- Account lockout threshold: 5–10 attempts
- Account lockout duration: 5–10 minutes
- Reset account lockout counter after: 10–15 minutes
Where to Configure
- Group Policy Management Console (GPMC)
Computer Configuration → Policies → Windows Settings → Security Settings → Account Policies → Account Lockout Policy
Advanced Considerations
- Use Fine-Grained Password Policies (FGPP) for high-risk accounts (admins, service accounts)
- Monitor Event IDs:
- 4625 (failed logon)
- 4740 (account locked out)
- Feed logs into your SIEM for correlation and alerting
Implementing This in Microsoft 365
In Microsoft 365, the model shifts significantly.
You don’t directly control “lockout duration” in the same way—because the platform is already applying smart lockout behavior.
Smart Lockout (Azure AD / Entra ID)
- Automatically tracks failed attempts
- Uses adaptive thresholds
- Differentiates between familiar and unfamiliar locations
What You Should Do Instead
1. Enable and Enforce MFA
- Conditional Access → Require MFA for all users (with staged rollout if needed)
2. Configure Conditional Access Policies
- Block legacy authentication
- Require compliant devices
- Apply geographic restrictions where appropriate
3. Monitor Identity Signals
- Azure AD Sign-in logs
- Risky sign-ins and users
- Integration with Defender for Identity / Sentinel
4. Tune Smart Lockout (if needed)
- Default threshold is typically sufficient
- Adjust only if you have a strong operational reason
The Bottom Line
A 15-minute lockout isn’t wrong.
It’s just incomplete.
- ✔️ It’s common
- ❌ It’s not a standard
- ⚠️ It can create more operational pain than security value
The real shift is this:
Stop treating account lockouts as a primary control. Start treating them as part of a layered identity defense strategy.
Because in today’s environment, the goal isn’t just to block access.
It’s to understand it.
* AI tools were used as a research assistant for this content, but human moderation and writing are also included. The included images are AI-generated.