 As many of my friends know, I have a slightly unhealthy obsession with the band Phish. Yes, that Phish from Vermont. The band whose reputation rides the coattails of Jerry Garcia & Co., traveling from city to city and playing wanked-out, 30-minute versions of songs to a bunch of patchouli and Birkenstock-wearing hippies.
As many of my friends know, I have a slightly unhealthy obsession with the band Phish. Yes, that Phish from Vermont. The band whose reputation rides the coattails of Jerry Garcia & Co., traveling from city to city and playing wanked-out, 30-minute versions of songs to a bunch of patchouli and Birkenstock-wearing hippies.
While only partially true, (or a majority for that matter) many “phans” or “glides” are actually quite resourceful and technically cunning.
Since the bands inception, (and taking a cue from The Grateful Dead) they’ve encouraged concert-goers to audio tape performances and trade those tapes, thus spreading their music far and wide.
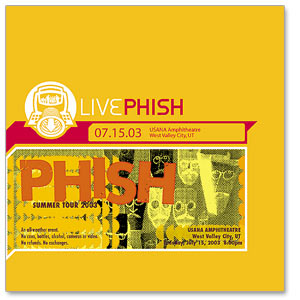
More recently, the band has included a free MP3 download code on each ticket and fans can actually listen to “crispy board” literally hours after the show has ended. A co-operative Google spreadsheet was established to document and source every known performance of the bands storied career and links to digital and audience performances. For those who aren’t interested in downloading every show in the band’s archive, one can actually obtain an external hard drive with the music and a handful of video taped performances already loaded.
If owning the entire catalog is too much music to sift through, fans have put together a number of compilations including “Machine Gun Trey,” “The Covers Project,” and a “Best Of’” version of the bands songs, chronologically — all labeled, sourced and ready to be downloaded into iTunes, with album art, of course.
While access to the band’s previous shows does quell the senses of their rabid fans, it does nothing but amplify the anticipation of upcoming tours. For a band that has a reputation of traveling from town to town, fans have come to expect Fall/Holiday/Spring/Summer Tour announcements to come about the same time each year.
Rumors began to speculate weeks ago about where and when the band might be playing this summer. Recon missions for tour dates along with some good old-fashioned social engineering confirmed a date here or there. Unsuspecting venue employees’ word about a “2 day hold on a venue” were placed together like puzzle pieces.
On February 28th, 2012, anticipation reached a near fevered pitch as the anticipated “Tour Dates at Noon” came and went without official announcement from the band and band’s management. With only 1 official date announced for Bonnaroo (a four-day, multi-stage camping festival held on a 700-acre farm in Manchester, Tennessee) on www.phish.com, internet savvy fans began a brute-force attack on the website, with surprisingly accurate results.
By changing the URL of the band’s website using the intelligence and rumored concert dates gathered during the social engineering exercise, a more accurate touring calendar began to reveal itself. A simple change to the URL didn’t reveal a “404 – Not Found” web page but the message “You don’t have access rights to this page.” Fans knew they were on to something and my Facebook friends began to make travel plans for the tour that hadn’t been officially announced. This “leg up” could possibly make the difference between a hotel bed close to the venue or car-camping on a hot July evening in a field somewhere nearby. It also could mean a difference in airfare, days off work, or even rental car availability.
The official announcement came shortly after 12:00 PM on Leap Day 2012, (which is perfectly fitting for Red, Henrietta, Leo, and Cactus) complete with a professionally produced video of Phish Drummer Jon “Greasy Physique” Fishman preparing like Rocky for an upcoming bout. At the bottom, of the video, the band’s summer tour plans streamed with surprising accuracy of what many knew 24 hours beforehand.
Not bad for bunch of stinky hippies!
