Launched in 2006, initially as a distributed honey pot product, HoneyPoint Security Server (HPSS) has grown well beyond the initial concept. Today HPSS is a platform of components woven into a tightly integrated, fully capable, extremely flexible threat detection product. Organizations around the world are using it as a means of early detection of internal and external attackers, malware outbreaks and signs of users poking around where they shouldn’t be. Mature organizations have leveraged the product as a means of deterring attacks through automated black holing of scanning hosts on their perimeter, embedded detective controls inside their web applications to cut off users violating their terms of service and gather real world threat metrics to feed back into their mature risk management initiatives.
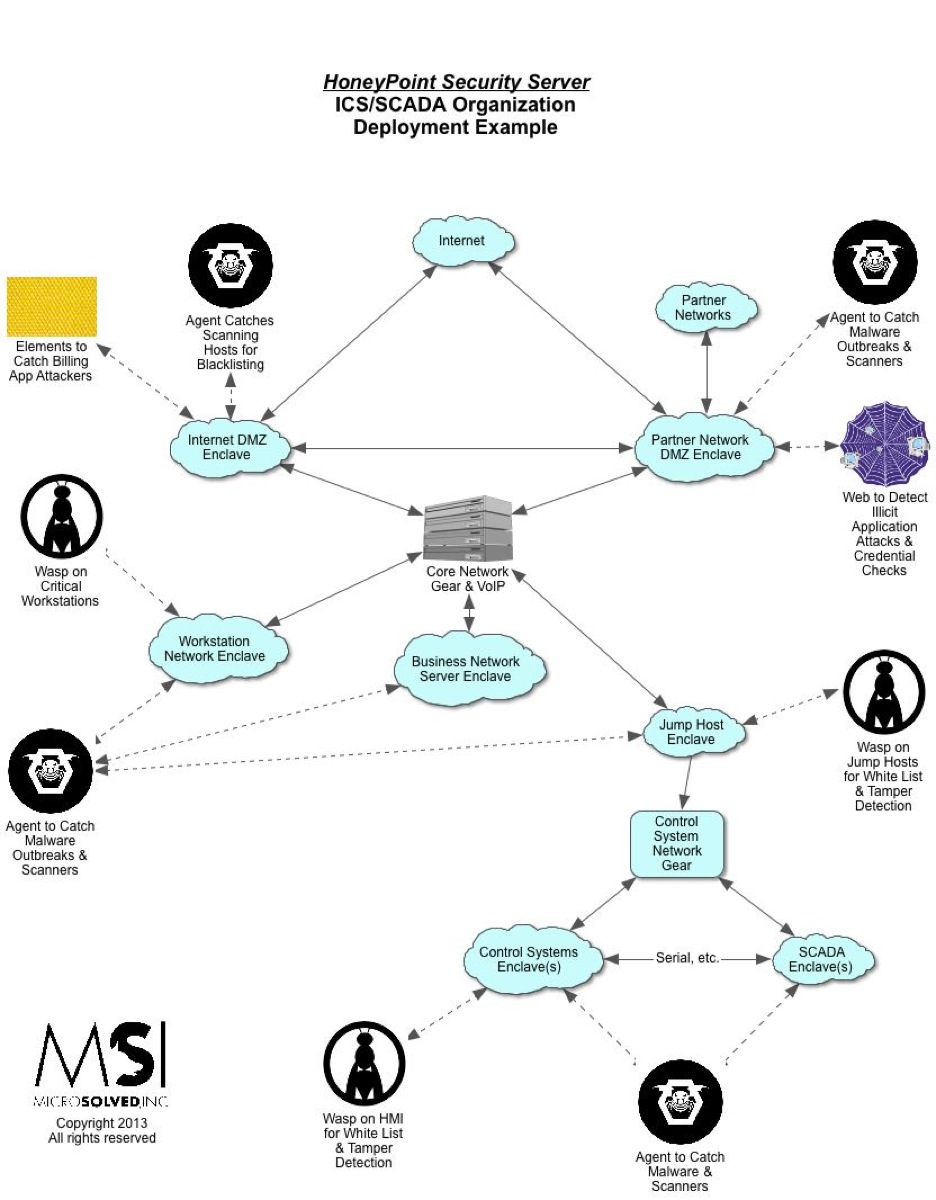
In the world of ICS/SCADA, HoneyPoint has found a quickly growing set of fans. HPSS can be deployed in a completely passive way that has no chance of interfering with critical operations, yet still brings incredible detection capability and vision into even the most sensitive of networks. ICS/SCADA environments have traditionally embraced the honeypot ideal, coining the term “canary” for these tools, but never before have they had such an easy to use, distributable, centrally monitored honeypot capability like HoneyPoint brings to the table.
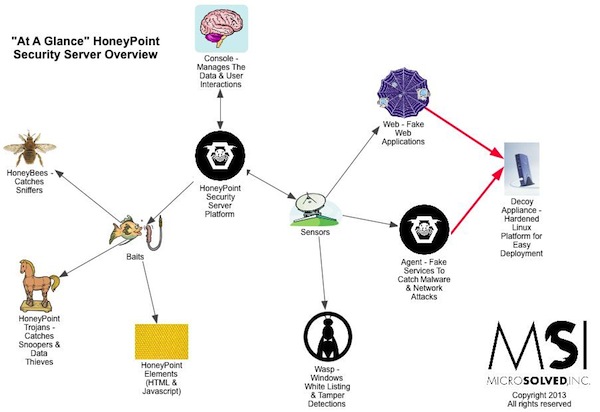
Over the next few months, we will be deep diving into each of the HPSS components, but for now, as a high-level overview, here is a quick and dirty explanation of each of them:
- HPSS Console – This is the central “brain” of the product. Designed as an easy to use GUI application, it receives the alerts detected by the sensor components and presents them to the user for analysis. It includes the “plugin” capability which allows for additional reporting and security automation based on the event data detected. The Console provides for “point and click” easy integration with SEIM products for clients who have deeper back-end data aggregation systems in place.
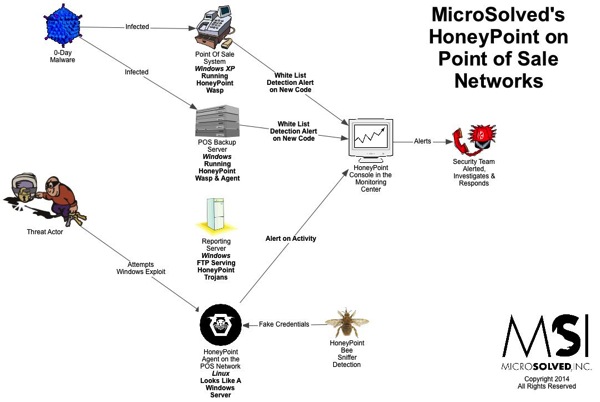
- HoneyPoint Agent – This is the original HoneyPoint detection capability. Agent creates “fake services” on the network that have no real use other than detection. Since the services aren’t real, any interaction with them is “suspicious at best and malicious at worst”. Agent is capable of emulating a great variety of services and is completely user configurable. Agent runs on Windows, Linux and OS X.
- Wasp – Wasp is HoneyPoint’s hybrid client for Windows systems. It offers many of the port dilation features of Agent, but layers on top of that a whitelisting detection mechanism, file change detection for key files and some simple heuristics to identify the most common signs of intrusion. Tiny footprint, immense flexibility, self tuning whitelisting and no interference with operations make it an excellent choice for critical infrastructure use.
- HoneyPoint Web – This is a completely emulated web environment with a mock up of applications that the organization uses. The entire environment is “fake” and studded with detection mechanisms that capture and measure attacker behavior, intent and capability. It might seem to be a new version of a banking application “accidentally” exposed to the Internet, or a replica of an HMI or maybe a login portal for Sharepoint/VPN or some other mechanism. What it really is is a detection mechanism for the good guys. Completely customized, able to detect the difference between a human attacker and most malware, it offers organizations a deeper, sneakier way to detect illicit behavior and measure the attacker attention various attack surfaces receive.
- HoneyElements – Embeddable HTML and Javascript objects that can be added to new or existing real web applications, these HoneyPoints extend detection into the layers of the application itself. Integrates well with automated response and attacker black holing defenses to stop attackers and those engaging in undesired behaviors in real time.
- HoneyBees – These work with Agent to simulate users authenticating to emulated services with plain text credentials. Organizations use this combination of tools to detect sniffing attacks and other attempts to harvest credentials off the wire or from network monitoring systems.
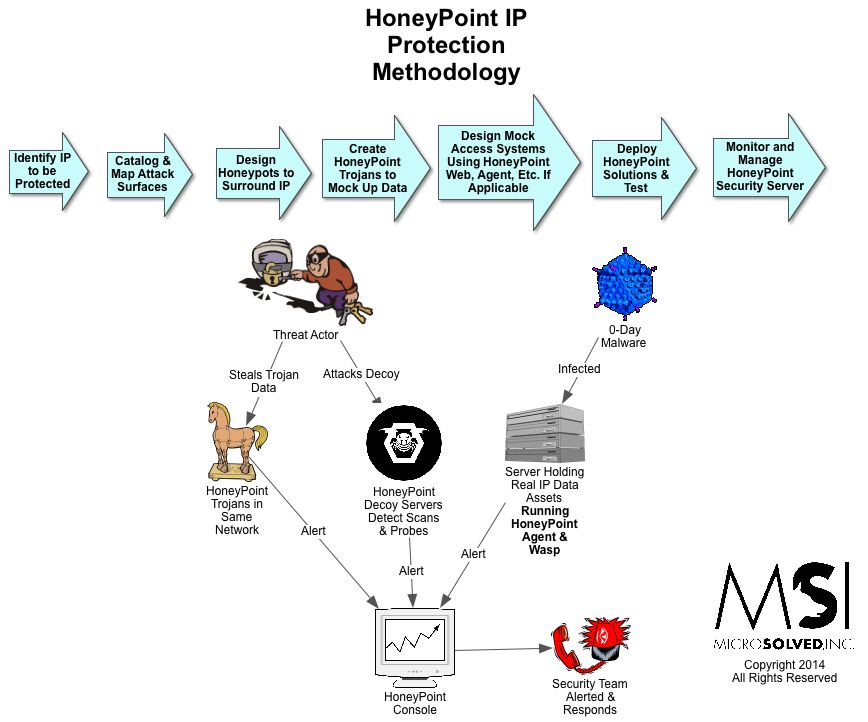
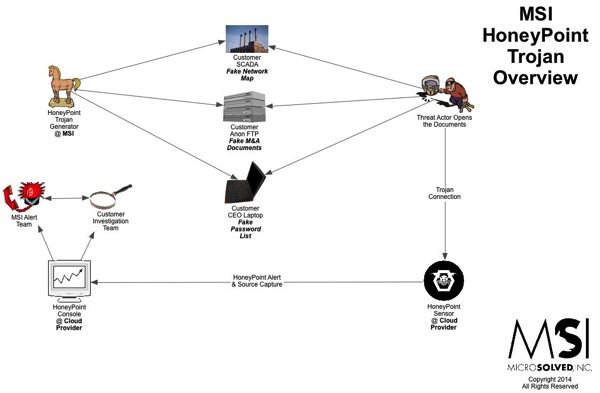
- HoneyPoint Trojans – Trojans are “fake” documents, applications or archives that appear to be real, but are actually detection mechanisms. For example, they might appear to be a PDF of some acquisition plans, while in reality they are armed with code to alert the security team when they have been opened or tampered with. Trojans use many of the same tactics as attackers, but instead of infection as a goal, they provide for detection and alerting.
- HoneyPoint Handler – The Handler is a mechanism for getting external events into the HoneyPoint data ecosystem. Organizations often use the handler to receive events generated by custom nuance detection scripts. For example, a script might routinely check for new files in a directory or new files that contain the call base64decode(). When the script identifies a new file, the script can send an alert to the Handler, which will create a standard HoneyPoint alert from the script’s data and send it to the Console for easy and standardized security event management.
- HoneyPoint Decoy Appliances – This is a set of hardened Linux powered devices that serve as an appliance for other components, usually Agent and Web. The appliances are available in three physical form factors (a rack mountable server, a mini-desktop, and a field deployable power substation solid state system) and/or a set of virtual appliances for most common virtualization platforms.
- HoneyPoint Proxy – Lastly, this component is designed to act as an alerting data aggregator to simplify firewall ACLs that might be deployed between DMZ segments, enclaves or other network segments. The proxy can receive events from HoneyPoints and send them on to the Console without the need to expose the Console to each individual HoneyPoint. This makes managing global and highly distributed deployments significantly easier.
To learn more about these components and how they can be leveraged to give your organization new, flexible and deep detection capabilities, give us a call. Our engineers would be glad to discuss the technical capabilities and an account executive would be happy to work with you to create a HoneyPoint deployment that meets your needs AND your budget. At MicroSolved, we are passionate about information security and HoneyPoint Security Server is just another that way it shows!