Happy holidays from the entire MSI team. We wish you a safe, joyous and prosperous holiday season!
As always, thanks for reading StateOfSecurity.com and for trusting MicroSolved, Inc. as your information security partner.

Happy holidays from the entire MSI team. We wish you a safe, joyous and prosperous holiday season!
As always, thanks for reading StateOfSecurity.com and for trusting MicroSolved, Inc. as your information security partner.
“Who watches the watchers?” is an often overheard question when we assess the information security program of clients. Way too often, the answer is either, “Huh?” or “No one, really.”. That’s a LOT of trust for an organization to place in an individual or small team.
At least in a small team, you hopefully have peers checking each other’s work. You do that right? You either rotate duties, have a peer review process or otherwise make sure that a second set of eyes from the team double checks critical work in a peer review methodology. That’s what mature teams do, and they do it both often and formally. This is a great control and an effective means to build cooperation between team members.
The problem gets harder when your security team (and/or IT team) is one person. Then it absolutely REQUIRES that someone, be it a manager, another department peer, an auditor or even a consultant checks their work periodically. After all, if they manage the servers, the firewall, the network, the intrusion detection and the logging, they essentially have complete control over the data and can do as they please without fear of getting caught. Now, that is not to say that folks in this role aren’t trustworthy. They usually are. The problem is that some are not and to further complicate the matter – it is often quite difficult to tell the difference between the honest and the dishonest humans. So, as we always say, “Trust, but verify…”. Implement an ongoing process for peer review, even if that peer is an auditor or consultant. Have them come in and double check the progress for this quarter. Ask them to spot check reports, logs and configurations. It’s not comprehensive, but it at least sends a message that someone is checking and just having someone checking different items often leads to interesting discoveries, usually not of a malicious nature, but often times something missed in the day to day.
How does your organization use peer review? What works and what hasn’t worked for you? Leave us a comment or drop us a line on Twitter (@lbhuston) and let us know.
Just a quick note to remind you that now is a good time to double check the on-call, vacation and coverage schedules for your infosec team members, all of the key members of your incident response team and the critical managers and department liaisons. It’s a good time to review and update your contact lists for these folks and to identify anyone who might be unavailable during the holidays double check that you have a secondary contact.
While we certainly hope that your team doesn’t have to respond to an incident during the holidays, it is not unheard of. So, a few moments of careful attention now, may save you some stress during an already stressful period.
Thanks for reading, have a great holiday season and stay safe out there!
We’ve been watching some interesting scans primarily hitting our HITME sensors in Asia for the last couple of weeks. The connection occurs on port 3131/TCP and contains the following request:
GET http://gameframe.net/headers HTTP/1.1
User-Agent: Opera/9.80 (Windows NT 6.1; WOW64) Presto/2.12.388 Version/12.10
Host: gameframe.net
Accept-Encoding: deflate, gzip
Proxy-Connection: Keep-Alive
Accept-Language: en-gb,en;q=0.5
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7
Pragma: no-cache
Cache-Control: no-cache
The scans we have seen seem to be originating primarily from Europe.
Have you seen similar scans and probes on this port? If so, please share with us in comments or via Twitter (@lbhuston).
In the meantime, it is worth checking your application logs if you have any custom applications deployed on this port, particularly exposed to the Internet. While we don’t see anything indicating an attack, review of anything exposed for errors or follow on attack traffic is suggested (it’s usually a good idea anyway).
Thanks for reading!
I had an interesting discussion on Twitter with a good friend earlier this week. The discussion was centered around information sharing in ICS/SCADA environments – particularly around the sharing of threat/attack pattern/vulnerability data.
It seems to us that this sharing of information – some might call it “intelligence”, needs to improve. My friend argues that regulation from the feds and local governments have effectively made utilities and asset owners so focused on compliance, that they can’t spare the resources to share security information. Further, my friend claims that sharing information is seen as dangerous to the utility, as if the regulators ever found out that information was shared that wasn’t properly reported “up the chain”, that it could be used against the utility to indicate “negligence” or the like. I can see some of this, and I remember back to my DOE days when I heard some folks talk along the same lines back when we showed up to audit their environments, help them with incidents or otherwise contribute to their information security improvement.
When I asked on open Twitter with the #ICS/#SCADA hashtags about what hampered utilities from sharing information, the kind Twitter folks who replied talked about primarily three big issues: the lack of a common language for expressing security information (we have some common languages for this (mitre’s work, VERIS, etc.)), legal/regulatory concerns (as above) and the perceived lack of mitigations available (I wonder if this is apathy, despair or a combination of both?).
I would like to get some wider feedback on these issues. If you don’t mind, please let me know either in comments, via private email or via Twitter (@lbhuston) what you believe the roadblocks are to information sharing in the ICS/SCADA community.
Personally, I see this as an area where a growth of “community” itself can help. Maybe if we can build stronger social ties amongst utilities, encourage friendship and sharing at a social level, empower ourselves with new mechanisms to openly share data (perhaps anonymously) and create an air of trust and equity, we can solve this problem ourselves. I know the government and industry has funded ISACs and other organizations, but it seems to me that we need something else – something more easily participatory, more social. It has to be easier and safer to share information between us than it is today. Maybe, if we made such a thing, we could all share more openly. That’s just my initial 2 cents. Please, share yours.
Thanks for reading, and until next time, stay safe out there!
This article builds on the What is HPSS? Series. The original overview article is here.
The HoneyPoint Security Server Console is the “brain” of the HoneyPoint product platform. It is the central component responsible for getting alert data from the sensors, tracking and maintaining the alert data, presenting it to the user and safely passing the essential alert data on to the automated plugins or other systems in the security event chain.
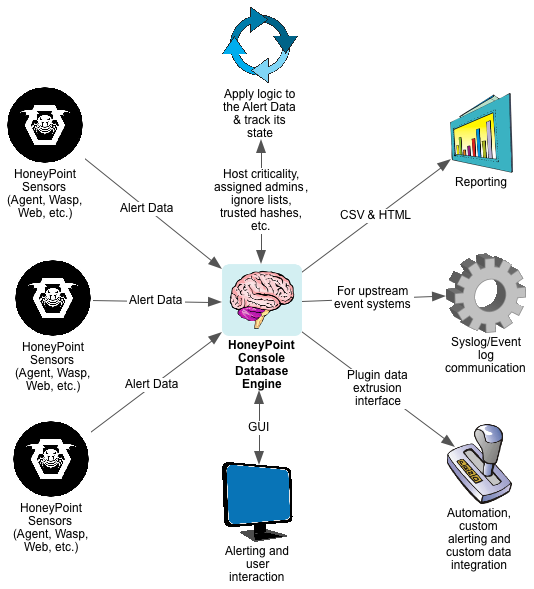
The Console is a GUI application that includes a built-in database engine for tracking Alert Data state and to empower reporting and analysis over time. Alert Data from the sensors are sent to the Console over TCP and the data is encrypted. The Console application runs on Windows, Linux and OS X.
Once the Console receives Alert Data from the sensors, it parses it to validate that the data is good and checks to see what actions it should take based on the alerting configuration, assigned admins list, ignored hosts lists, and other trust rules in place.
It then presents the alert data to the appropriate mechanisms, alerting users, passing the desired elements of the alert data to syslog/event log on the Console system for upstream processing by SEIMs or other event tools. The Console also passes certain event data as determined by the configuration into the “plugins mechanism”.
The plugins then execute the desired operations on the data, easily allowing the security team to further extend reporting to custom event handlers or perform automated responses. This flexible solution empowers the security team to integrate HoneyPoint Security Server fully into whatever technology platform/response process they desire or have in place.
Reporting from the Console is very simple. The included reporting engine can create a wide variety of canned reports in either CSV or HTML format, ensuing that the data in the HoneyPoint system is easy to use. Additionally, other reporting tools like Crystal Reports or the like, or even languages like PERL, Python or Ruby, can easily attach to the Console database to create whatever types of custom reports you desire.
All in all, HoneyPoint Security Server was designed to make it easy to use and yet flexible enough for the most demanding and mature infosec teams. The console interface is friendly, functional and easily understandable. Most teams require less than a 30 minute walk through before they are off and running with the basic detection power HoneyPoint provides. When they get comfortable with the system, they quickly master the plugins meta-language and are soon automating large groups of detection and response tasks.
To learn more about HoneyPoint Security Server or to get a demo, please contact us. We would be happy to walk you through the product and discuss how it might fit into your environment. There is even a free for personal use “Community Edition” available to get you started or to let you experience the power, ease and flexibility of the platform yourself. Just give us a call to learn more about HoneyPoint Security Server Console. You’ll be glad you did!
Launched in 2006, initially as a distributed honey pot product, HoneyPoint Security Server (HPSS) has grown well beyond the initial concept. Today HPSS is a platform of components woven into a tightly integrated, fully capable, extremely flexible threat detection product. Organizations around the world are using it as a means of early detection of internal and external attackers, malware outbreaks and signs of users poking around where they shouldn’t be. Mature organizations have leveraged the product as a means of deterring attacks through automated black holing of scanning hosts on their perimeter, embedded detective controls inside their web applications to cut off users violating their terms of service and gather real world threat metrics to feed back into their mature risk management initiatives.
In the world of ICS/SCADA, HoneyPoint has found a quickly growing set of fans. HPSS can be deployed in a completely passive way that has no chance of interfering with critical operations, yet still brings incredible detection capability and vision into even the most sensitive of networks. ICS/SCADA environments have traditionally embraced the honeypot ideal, coining the term “canary” for these tools, but never before have they had such an easy to use, distributable, centrally monitored honeypot capability like HoneyPoint brings to the table.
Over the next few months, we will be deep diving into each of the HPSS components, but for now, as a high-level overview, here is a quick and dirty explanation of each of them:
To learn more about these components and how they can be leveraged to give your organization new, flexible and deep detection capabilities, give us a call. Our engineers would be glad to discuss the technical capabilities and an account executive would be happy to work with you to create a HoneyPoint deployment that meets your needs AND your budget. At MicroSolved, we are passionate about information security and HoneyPoint Security Server is just another that way it shows!
Just a quick reminder that December’s #CMHSecLunch is Monday, December 10th from 11:30am to 1:00pm at the North Market upstairs near the elevators.
Come by, hang out, see old friends, chat about infosec and tech. Grab some amazing lunch.
See you there. Use the #CMHSecLunch on Twitter and please let folks know about it and to expect you. Open to all and free to attend!
Question from a reader: What should I be paying attention to the most with regards to web applications? My organization has a number of Internet facing web applications, but I don’t even know where to start to understand what the risks and exposures might be.
Adam Hostetler responds:
The first thing I would do is to identify what the applications are. Are they in house developed applications, or are they something like WordPress or another framework? What kind of information do they store (email addresses, PII, etc)? If they are in house or vendor applications, have they been assessed before? With a little knowledge of the applications, you can start building an understanding of what the risks might be. A great resource for web application risks is the OWASP project. https://www.owasp.org
Phil Grimes adds:
When it comes to web applications, I always promote a philosophy that I was raised on and continue to pound into my kid’s heads today: Trust but verify. When an organization launches an internet facing application there is an immediate loss of control on some level. The organization doesn’t know that the users accessing the application are who they say they are, or that their intentions are “normal”. Sure, most people who encounter the app will either use it as intended or if they access the app inadvertently, they may just mosey on about their merry way. But when a user starts poking around the application, we have to rely on the development team to have secured the application. Making sure identity management is handled properly will help us ensure our users are who they say they are, and validating all data that a user might pass to the application becomes an integral part of security to ensure possible attacks are recognized and thwarted.
John Davis comments:
I would say that the most important thing is to ensure that your Internet facing web applications are coded securely. For some time now, exploiting coding weaknesses in web applications has been one of the leading attack vectors exploited by cyber criminals to compromise computer networks. For example, poor coding can allow attackers to perform code injection and cross site scripting attacks against your applications. The Open Web Application Security Project (OWASP), which is accessible on the Internet, is a good place to learn more about secure web application coding techniques. Their website contains lots of free tools and information that will help your organization in this process. There are also professional information security organizations (such as MicroSolved) that can also provide your organization with comprehensive application security assessments.
As always, thanks for reading and let us know if you have questions for the experts.