Category Archives: Threat Intelligence
Hiring Data Analysts Who Love Security
MSI is growing again! We are interested in talking to folks about a full time position in our Columbus HQ to help our Intelligence Team.
If you dig being heads down with data, performing deep research and chasing threats around the Internet, this is the gig for you! These folks will be focused primarily on threat profiling, research of companies, crime rings and security news from around the world. The job requires you be familiar with Linux, have an understanding of information security and to be a power user of the Internet. You should also enjoy python, BASH scripting, command line kung fu and staying bleeding edge current on security happenings. Light public speaking on webinars and conference calls, familiarity with the Mac and excellent writing skills are also preferred.
MSI is an interesting place to work. Our team is seriously dedicated to helping our clients. We are known for doing excellent work, thinking outside the box, going deep into a problem and laser focusing on customer success. Our conversations among team members are fast and full of high density data exchange. It is exciting, fulfilling and demanding work, but we do it with joy, precision and mindful innovation!
Sound like something you might enjoy? If so, get in touch. Send your resume and a cover letter that explains why you are the best choice for our team to info@microsolved.com. You can also touch base with me on Twitter if you have questions (@lbhuston). We hope to hear from you if you truly love deep diving on data and hammering out the truth from content all around the web!
PS – Don’t worry, we know we have to train you. We are looking for people with strong core skills, an eagerness to learn and out of the box thinking. We’ll teach you the rest… 🙂
Lots of PHP Web Shells Still Circulating
Many PHP-based web shells are still making the rounds, and while many of them are based on old code, mutations, customizations and updates abound. They are so common, that new variants and modified versions are often seen at the rate of about 10 a day in our TigerTrax Threat Intelligence systems and honeypots.
Variants exist for a wide variety of platforms and human languages, many with some very nasty features and even some cool ASCII art. There are many variants for attackers to choose from for just about any of the popular PHP-based content management platforms. From WordPress to Joomla and beyond to the far less common apps, there are easily used exploits and shell kits widely available.
If you run a PHP-based site or server, it’s a good idea to keep an eye on the file system changes and watch closely for new files being uploaded or added. Pay particular attention to those using the “base64_decode” function, since it is so common among these tools.
Thanks for reading, and until next time, stay safe out there!
Telnet!? Really!?
I was recently analyzing data from the HITME project that was collected during the month of January. I noticed a significant spike in the observed attacks against Telnet. I was surprised to see that Telnet was being targeted at such a high rate. After all, there can’t be that many devices left with Telnet exposed to the internet, right?
Wrong. Very wrong. I discovered that there are still MILLIONS of devices with Telnet ports exposed to the internet. Due to Telnet’s lack of security, be sure to use SSH as opposed to Telnet whenever possible. If you absolutely must control a device via Telnet, at least place it behind a firewall. If you need to access the device remotely, leverage the use of a VPN. Finally, be sure to restrict access to the device to the smallest possible IP range.
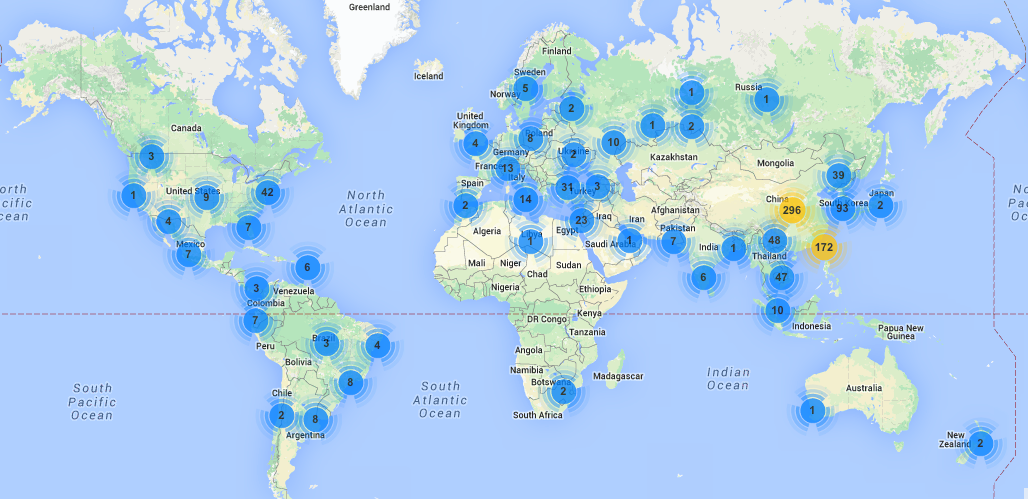
The map below shows the geographical locations and number of attacks against Telnet that we observed last month. If you need any help isolating Telnet exposures, feel free to contact us by emailing info <at> microsolved.com.
Social Media Targeting: A Cautionary Tale
I was recently doing some deep penetration testing against an organization in a red-team, zero knowledge type exercise. The targets were aware of the test at only the highest levels of management, who had retained myself and my team for the engagement. The mission was simple, obtain either a file that listed more than 100 of their key suppliers, or obtain credentials and successfully logon to their internal supply system from an account that could obtain such a file.
RansomWeb Attacks Observed in HITME
Unfortunately, the destructive nature of Ransomware has taken a new turn for the worse. A new technique called RansomWeb is affecting production web-based applications. I recently analyzed data from the HITME project and observed several RansomWeb attacks against PHP applications. I can only assume the frequency of these attacks will increase throughout the year. As a former Systems Administrator, I can definitively say that it would be a nightmare to bring an application back online that was affected by this variant of Ransomware. Due to RansomWeb’s destructive nature, it is important to ensure that your organization is actively working to prevent RansomWeb from destroying any critical systems.
The attackers begin the RansomWeb process by exploiting a vulnerability within a web server or web-based application. Once the server or application have been exploited, the attackers slowly begin encrypting key databases and files. Once the encryption is complete, the hackers shut down the website/application and begin to demand ransom in exchange for the decryption of the corporation’s files. Unfortunately, the attackers have even perfected using this process to encrypt system-level backups.
To prevent RansomWeb from affecting your organization, please be sure to complete the following steps on a regular basis:
- Perform regular vulnerability assessments and penetration testing against your critical applications and servers.
- Audit your application and system logs for any irregular entries.
- Verify that you are performing regular application and system backups.
- Be sure to test the backup/ restore process for your applications and systems on a regular basis. After all, your backup/ DR process is only as effective as your last successful restore.
If you would like to discuss how we can help you prevent RansomWeb from affecting your production applications, do not hesitate to contact us by emailing info <at> microsolved.com
Recently Observed Attacks By Compromised QNAP Devices
Despite the fact that the Shellshock bug was disclosed last fall, it appears that a wide variety of systems are still falling victim to the exploit. For example, in the last 30 days, our HoneyPoint Internet Threat Monitoring Environment has observed attacks from almost 1,000 compromised QNAP devices. If you have QNAP devices deployed, please be sure to check for the indicators of a compromised system. If your device has not been affected, be sure to patch it immediately.
Once compromised via the Shellshock bug, the QNAP system downloads a payload that contains a shell script designed specifically for QNAP devices. The script acts as a dropper and downloads additional malicious components prior to installing the worm and making a variety of changes to the system. These changes include: adding a user account, changing the device’s DNS server to 8.8.8.8, creating an SSH server on port 26 and downloading/installing a patch from QNAP against the Shellshock bug.
The map below shows the locations of compromised QNAP systems that we observed to be scanning for other unpatched QNAP systems. If you have any questions regarding this exploit, feel free to contact us by emailing info <at> microsolved.com.
Spike in HITME NTP Probes Following Recent Exploits

Benefits of using TigerTrax to Monitor Your Industry
Have you ever wanted to know what is being said in regards to your business or product line on social media? How about getting the scoop on a company prior to your big merger or acquisition? Perhaps you have a need for continual code of conduct monitoring for your business or franchise. These are but a few of the things that we at MicroSolved, Inc can provide for you and your company! MicroSolved has a whole host of proprietary software including TigerTrax, that will give your company an edge over your competition!
With our TigerTrax platform we can help provide you with a competitive advantage by receiving actionable intelligence about your product line from the social media hemisphere. Imagine scouring the entire population of Twitter, which boasts some 645 million registered users with over 115 million active users monthly. That is an enormous market that you can tap into with our help. A market where you can see where you think that your product line may be heading versus what people are actually talking about in regards to your product line. Imagine being able to fine-tune your marketing campaign based on our intelligence gathering ability!
In every business there are times whether for a short duration or a long term one where you may want us to provide you with code of conduct information about your employees. Perhaps their contracts clearly state what sort of things they may or may not post on social media and the internet; but also and more importantly you may want to know what everyone else is posting about them. We can help provide you that information. Our TigerTrax platform does in minutes what takes a roomful of employees days or weeks to do and in a very short time you can have actionable information that may be used to help protect your companies brand!
As you can see TigerTrax is a wonderful tool in your arsenal for providing actionable data that will enable you to adjust your marketing campaign or perform ongoing code of conduct monitoring. We can also perform threat intelligence, assess whether your intellectual property has been leaked online, and of course perform brand intelligence. As you can imagine we are only scratching the surface of what we at MicroSolved, Inc and the TigerTrax platform can do for you. So please if you need any assistance for your company feel free to contact us by sending an email to: info@microsolved.com.
This post by Preston Kershner.
5 Ways My Medical Background Makes Me a Better Intelligence Analyst
When I first started for MicroSolved, Inc.(MSI), I wasn’t sure what to think, but now that I have been here for nearly three months I feel I am starting to get the hang of what it is to be an intelligence analyst. At least a little bit anyhow. Now mind you I am not your typical intelligence analyst, nor am I a new college graduate, but rather I am coming to MSI from the health care industry with over twenty years of work experience in that industry. This was a completely different mindset, with a whole host of new things for me to experience and learn. For me this was totally refreshing and exactly what I wanted and more importantly, needed! There are a few things that I have noticed in my short time here that could be considered pearls of wisdom rather than actual characteristics of a good employee that I feel make me a good intelligence analyst for MSI. Perhaps they are one and the same. At least that is my hope 😉
First, while I am not a seasoned IT professional like so many others that I work with, I am not naive to the fact that there are deadlines and expectations thrust upon all of us. This in my opinion is no different than in being in the hospital setting where people expect you to act quickly and in the best interests of your patient at all times. Couldn’t we say the same is true working for a company like MSI? In that it is the expectation to be professional, performing your best at all times, and the like? I would like to think that is what I strive for.
After thinking a bit longer perhaps it is that we share a tenacity for getting to the bottom of whatever mystery that we are looking at. Whether it is a series of questions that we may be asking our patients in an effort to try to figure out what ailment they be suffering from. This is not unlike when we are looking for a key bit of code for an algorithm to help us do our work more efficiently. Regardless, it is this mentality of never giving up! To keep fighting, keep looking, to keep trying. Just keep chipping away at it.
I think the next characteristic would have to be patience. Something that we all have often heard from our grandparents growing up as children. Something that in my mind and in my experience has played a provocative role in both my dealings with patients, their families and with challenging projects in the IT world. Now while as I previously stated in the above paragraph that tenacity plays a role, I also think having a measure of patience does too. There are times in the medical world where even the most experienced physician stands there for a moment and scratches his or her head and says “I don’t know”. Now to a patient that is the last thing that they want to here, but sometimes we truly have to “wait and see”. Sometimes grandma was right! There have been times while working on projects with MSI, where sitting back even if it’s just a few moments, allowed me to gain a better “bird’s eye view” of a given project and really helped me figure out what it was that I was looking for and ultimately aided the project.
Another area that I think gives me an edge would be that I am willing to go the extra mile and I am not afraid to work hard to attain my goals. It isn’t enough to just punch a clock or be mediocre! I have told this to my children, my patients and my friends. Never give up, always work your butt off for what you want in life! It may take time for what you want to come to fruition, but if you’re willing to put the time, energy and effort into it, then it will come! It takes sacrifice to get to your goals. Others will recognize your efforts and aid you in your path. That’s what I feel MSI has done and is continuing to do for me!
Lastly, laugh! I have not laughed so hard in any of my previous work experiences as compared to working for MSI these past few months. Don’t get me wrong there were plenty of wonderful times, but here at MSI it is a whole new animal! Yes, we work hard, but I think having a healthy sense of humor and a desire to see others laugh is what really sets MSI apart. If you are down, they help pick you up! So often we spend our work lives with people that aren’t our family for hours on end. Shouldn’t we have some fun while we work? If you are lucky enough you do. Then, by choice those people that aren’t your family start to become them and find a place in your heart. Then, your work doesn’t seem like work anymore.
Yes it’s true that I am new to the world of information technology as a career choice, but that doesn’t mean that I don’t have some very real life experiences to draw upon. Remember, it is a combination of work ethic, tenacity, patience, a sense of humor and ultimately a willingness to never give up. These are the things that will make you successful, not only in your career path, but in life as well. These are my little pearls of wisdom, just a few tidbits of information to help you get to where you want to be in life. Who knows it might even be right here at MSI.
This post by Preston Kershner.