In the not too-distant past I was involved in helping secure the information infrastructure of a major EDI “VAN”.
How’s that for gibberish? Some definitions are in order:
EDI = “Electronic Data Interchange”. Effectively, a collection of standards for the encoding of documents such as invoices, purchase orders, bills of lading, medical information, and – it seems – information pertaining to the business of buying, selling and moving natural gas.
EDI dates from the 1970’s. It took advantage of pre-Internet communication mechanisms but quickly was adapted to the Internet and likely will be to blockchain.
EDI “trading partners” can communicate directly, but often they rely on third-party EDI specialists to handle communication with their various trading partners. These are the EDI “Value Added Networks” (VAN).
EDI is the unsung hero of modern commerce.
Everything we buy or sell has a secret life as an EDI document. Usually a number of them.
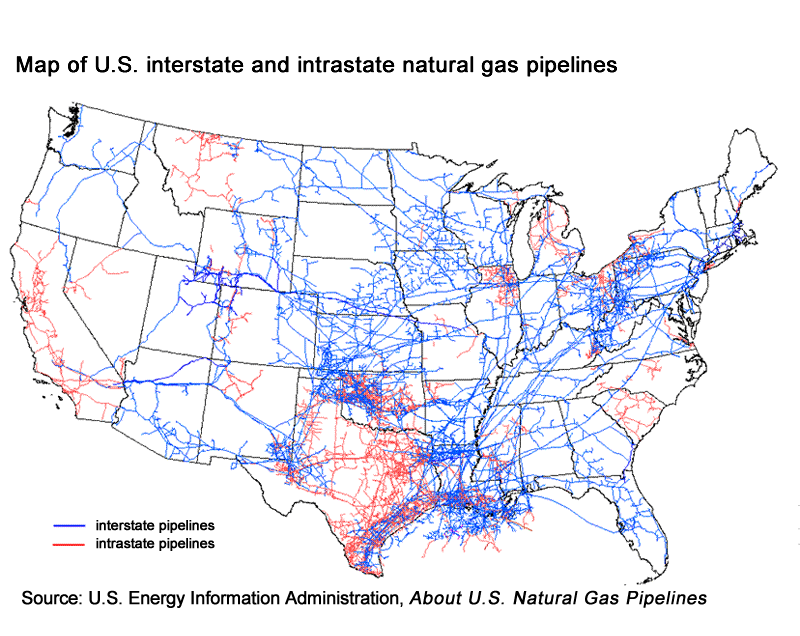
Not surprisingly, natural gas pipeline companies use EDI in the running of their business, communicating information about availability and pricing to their customers and government. A few months ago, the business of some natural gas pipeline companies was disrupted by the sudden unavailability of those EDI services.
The attack, in March 2018, was directed against a central provider of EDI services to several major natural gas pipeline operators. Although it did not affect actual in-field operations, it did stop all normal business traffic for several days, causing confusion and a fall-back to alternate communication mechanisms.
Of greater concern was the loss of potentially sensitive information about internal business structure, all of which can be inferred from the ebb and flow of EDI data. Such information can be invaluable to an attacker and in this case can be an aid in eventually attacking actual pipeline operations.
The point here is that it is easy to view such operations as strictly an ICS security concern, and that with proper segmentation of business from ICS infrastructure all will be well.
I’ve had some experience in that ICS world over the last few years and know that segmentation is often incomplete at best. Even when segmentation is present, your business can still be vulnerable to attacks on exposed business systems that have process flow links to ICS.
What to do?
- Know how you use EDI and what your supporting infrastructure is.
- Know who your EDI providers are and what security measures they employ
- Do a business impact analysis of your EDI environment. What happens if it goes away?
- Ensure you really do have segmentation of your business and ICS worlds. Make sure the places they touch are known, secured, and monitored.
See:
EDI defined:
https://www.edibasics.com/what-is-edi
https://en.wikipedia.org/wiki/Electronic_data_interchange
https://www.edibasics.com/edi-resources/document-standards
Natural Gas Industry Usage of EDI:
https://www.naesb.org/pdf4/update031413w4.docx
Quote: “The NAESB wholesale natural gas cybersecurity standards facilitate an infrastructure of secure electronic communications under which the electronic transmission of data via EDI or browser based transactions is protected. There are more than fifty separate transactions identified for nominations, confirmations, scheduling of natural gas; flowing gas transactions including measurement, allocations, and imbalances; invoicing related transactions including invoices, remittances, statement of account; and capacity release transactions.”
http://www.rrc.texas.gov/oil-gas/applications-and-permits/oil-gas-edi-filing-deadlines/
The Attack:
https://www.eenews.net/stories/1060078327
http://securityaffairs.co/wordpress/71040/hacking/gas-pipeline-operators-hack.html
EDI Security:
https://www.acsac.org/secshelf/book001/18.pdf
Quote: “EDI security appears at several interrelated stages:
- The user/application interface,
- EDI applications and value added services,
- The processing (both batch and interactive) and storage of EDI messages,
- The communication of these messages in an open systems environment”
If you would like to know more about MicroSolved or its services please send an e-mail to info@microsolved.com or visit microsolved.com.