I had an interesting conversation this week over email with a security admin still fighting Conficker.
I had an interesting conversation this week over email with a security admin still fighting Conficker.
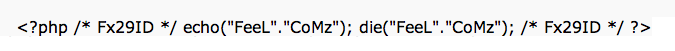
If you haven’t recalled Conficker in a while, take a moment and read the wikipedia entry here: (http://en.wikipedia.org/wiki/Conficker). Back in 2008, this nasty bugger spread across the net like wild fire. It was and is, quite persistent.
Back in those days, we even put out a free version of HoneyPoint called HPConficker to act as a scatter sensor for detecting infected hosts on networks around the world. That tool expired eventually, and to be honest, we stopped really tracking Conficker back in 2010 to move on to studying other vectors and exploits. I hadn’t even thought about the HPConficker tool since then, until this week.
In order to help this admin out as they battled the worm, I came in on a vacation day, dug the old code out of the source vault and updated it to run through the end of 2012. I then built a quick compile, zipped it (in my hurry forgetting to remove the OS X file noise) and sent it on to the sales person who was helping the client directly. When I heard that the zip file with OS X noise was a problem, I quickly cleaned the zip and sent it back up to the server for them to re-download, install and use. Sadly, I haven’t yet had time to build a readme file or the like, but the tool is pretty easy to use. Unzip it with folder extraction enabled, execute it and follow the GUI instructions. I haven’t heard back from my new security admin friend, but I hoped it helped them fight the good fight.
I took a couple of key points from this: 1) Conficker is still around and causing trouble; and 2) Helping people with HoneyPoint is still one of the core reasons I do what I do.
I may not say it often enough, but, thanks to all of you for playing with my toys. Since 2006, the knowledge gained, the insights and the outright chance to help people with my software has been a great joy. I look forward to pursuing it for many years to come.
Keep playing with HoneyPoint. Keep talking to us. We want to engage, and we want to help YOU solve YOUR problems. At the core, that’s what MSI is all about. As always, thanks for reading and stay safe out there!
PS – We haven’t decided if we are going to release the tool again. If you want it and it can help you, drop me a line in the comments, send me a tweet (
@lbhuston) or get in touch. Even if we don’t push it out in public on the site, it’s here if you need it…