- The “3 Legged Model” or “single firewall” – where the DMZ segment(s) are connected via a dedicated interface (or interfaces) and a single firewall implements traffic control rules between all of the network segments (the firewall could be a traditional firewall simply enforcing interface to interface rules or a “next generation” firewall implementing virtualized “zones” or other logical object groupings)
- The “Layered Model” or “dual firewall”- where the DMZ segment(s) are connected between two sets of firewalls, like a sandwich
Category Archives: Risk Management
Clients Finding New Ways to Leverage MSI Testing Labs
Just a reminder that MSI testing labs are seeing a LOT more usage lately. If you haven’t heard about some of the work we do in the labs, check it out here.
One of the ways that new clients are leveraging the labs is to have us mock up changes to their environments or new applications in HoneyPoint and publish them out to the web. We then monitor those fake implementations and measure the ways that attackers, malware and Internet background radiation interacts with them.
The clients use these insights to identify areas to focus on in their security testing, risk management and monitoring. A few clients have even done A/B testing using this approach, looking for the differences in risk and threat exposures via different options for deployment or development.
Let us know if you would like to discuss such an approach. The labs are a quickly growing and very powerful part of the many services and capabilities that we offer our clients around the world!
MachineTruth As a Validation of Segmentation/Enclaving
If you haven’t heard about our MachineTruth™ offering yet, check it out here. It is a fantastic way for organizations to perform offline asset discovery, network mapping and architecture reviews. We also are using it heavily in our work with ICS/SCADA organizations to segment/enclave their networks.
Recently, one of our clients approached us with some ideas about using MachineTruth to PROVE that they had segmented their network. They wanted to reduce the impacts of several pieces of compliance regulation (CIP/PCI/etc.) and be able to prove that they had successfully implemented segmentation to their auditors.
The project is moving forward and we have discussed this use case with several other organizations to date. If you would like to talk with us about it, and learn more about MachineTruth and our new bleeding edge capabilities, give us a call at 614-351-1237 or drop us a line via info <at> microsolved <dot> com.
Involved in M&A Activity? MSI has a full M&A Practice
MSI’s specialized offerings around Mergers & Acquisitions are designed to augment other business practices that are common in this phase of business. In addition to general security consulting and intelligence about a company from a “hacker’s eye view”, we also offer deeply integrated, methodology-driven processes around:
- Pre-negotiation intelligence
- This offering is designed to help the purchasing organization do recon on their prospect for purchase. Leveraging techniques like passive assessment, restricted individual tracing, supply chain analysis, key stakeholder profiling and history of compromise research, the potential purchasing company can get deep insights into the security posture and intellectual property integrity of the company they are considering for acquisition. All of this can be done passively and prior to a purchasing approach or offer. Insights from this service can be a useful tool in assessing approach and potential valuation.
- Pre-integration assessments
- Once the ink on the paperwork is dry, the organizations have to learn to live and work together. One of the most critical links, is the joining of the two IT infrastructures. In this service, our experts can perform assessments to analyze the new company’s security posture against the baseline standards of the purchasing organization. A gap analysis and road map for compliance can be provided, and if desired, MSI can serve as oversight for ensuring that the mitigations are completed as a condition for network interconnection and integration. Our team has performed these services across a variety of M&A completions, including multi-national and global Fortune 500 organizations.
- Post-purchase threat intelligence
- MSI can also create mechanisms post-purchase to identify and respond to potential threats from inside the newly acquired organization. Our counter-intelligence and operational security techniques can help organizations identify potential internal bad actors or disgruntled new employees that could be seeking to damage the acquirer. We have created these solutions across a myriad of verticals and are quite capable of working in international and other highly complex environments.
To learn more about these specific offerings, click on the links above. To discuss these offerings in more detail, please contact your account executive for a free consultation.
Plus, we also just added some new capabilities for asset discovery, network mapping and traffic baselining. Check this out for some amazing new ways we can help you!
Operation Hardened Buckeye
MSI is pleased to announce the immediate formation and availability of Operation Hardened Buckeye!
This special program is dedicated to assisting Ohio’s Rural Electrical Cooperatives.
MSI will set up aggregated groups of Electrical Cooperatives and perform services and offer tools to the groups en-masse at discounted rates, as if they were one large company. Essentially, this allows the co-ops to leverage group buying, while still receiving individual reports, software licenses and overall group-level intelligence & metrics.
MSI will offer a package consisting of the following:
- External Vulnerability Assessment with aggregated executive level reports/metrics & individual technical detail reports
- An aggregated Targeted Threat Intelligence engagement with individual notifications of critical findings and an aggregated intelligence report for the group
- 3 HoneyPoint Agent licenses and a console license per co-op that participates
- Deep discounts to individual co-ops who desire application assessment, internal vulnerability assessments, wireless assessments or other MSI professional services (including MSI::Vigilance & ICS Network Segregation Services)
- Deep discounts for ongoing assessments and targeted threat intelligence as a service
Caveats: All assessments will be performed at the same time. Co-ops must each sign onto a common MSA. Each co-op will be billed for the total of the package divided by the number of participating co-ops. Co-ops must provide accurate IP address ranges for their external assessment.
This enables the co-ops to have a security baseline of their security posture performed, including aligning their current status against that of their peers. It also allows for each of the co-ops to deploy a HoneyPoint Agent in their DMZ, business network and control network for detection capabilities. The targeted threat intelligence will provide them with an overall threat assessment, as well as identifying individual targets that have either already been attacked or are likely to provide easy/attention raising targets for future attacks.
We will be holding a webinar for those interested in participating on Thursday, May 21, 2015. You can register for this event here. You can also download the flyer about the program here.
For more information, please contact Allan Bergen via the email below or call (513) 300-0194 today!
Email: sales@microsolved.com
First Step After Breach
Discovering an information security breach can be a shock! Picture it: you are enjoying a regular work day and WHAM! Suddenly you are at the center of an incident that could possibly affect the future of the company and perhaps your own future as well. It’s easy to panic. You know if you don’t do the right thing, right now, bad things are sure to rain down on you. So, what is the very first thing that you should do?
Go immediately to your incident response plan, of course! After all, that is the reason your company has put together an IR plan and team in the first place; to plan for contingencies so that personnel don’t go off half-cocked and lose vital data and evidence.
But is your plan clear enough that regular system users or even help desk personnel know what to do first without having to thumb through a hundred pages of plan? If not, perhaps a simple little trick we use in our incident response plans will work for you.
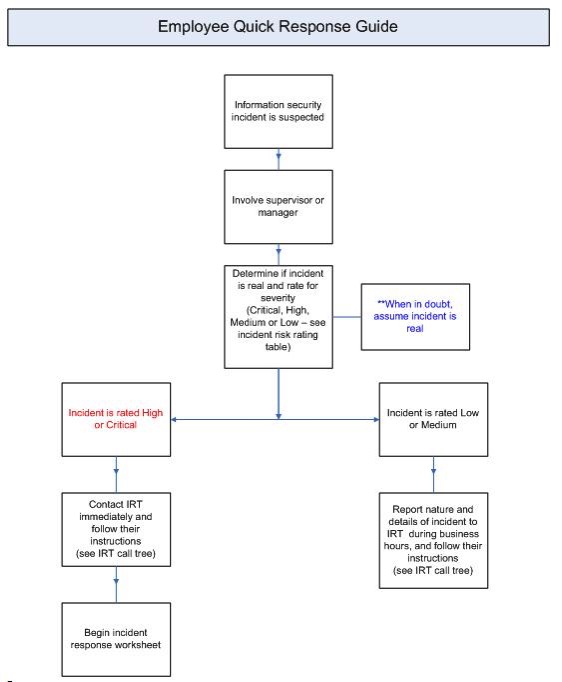
The very first thing you see when you open one of our incident response plans are employee and incident response team Quick Response Guides (see the example of an employee guide below-the IRT guide is similar, but more complex).
I know from my military experience that having checklists such as the Quick Response Guides in place truly cuts down on mistakes and helps calm personnel during difficult situations. Why not see if they can also improve your response quality?
You can download the pocket guide here.
Thanks to John Davis for this post.
State Of Security Podcast Episode 4
We are proud to announce the release of State Of Security, the podcast, Episode 4. This time around I am hosting John Davis, who riffs on policy development for modern users, crowdsourcing policy and process management, rational risk assessment and a bit of history.
Give it a listen and let us know what you think!
Thanks for supporting the podcast!
How to Use Risk Assessment to Secure Your Own Home
Risk assessment and treatment is something we all do, consciously or unconsciously, every day. For example, when you look out the window in the morning before you leave for work, see the sky is gray and decide to take your umbrella with you, you have just assessed and treated the risk of getting wet in the rain. In effect, you have identified a threat (rain) and a vulnerability (you are subject to getting wet), you have analyzed the possibility of occurrence (likely) and the impact of threat realization (having to sit soggy at your desk), and you have decided to treat that risk (taking your umbrella) – risk assessment.
However, this kind of risk assessment is what is called “ad hoc”. All of the analysis and decision making you just made was informal and done on the fly. Pertinent information wasn’t gathered and factored in, other consequences such as the bother of carrying the umbrella around wasn’t properly considered, other treatment options weren’t considered, etc. What business concerns and government agencies have learned from long experience is that if you investigate, write down and consider such factors rationally and holistically, you end up with a more realistic idea of what you are really letting yourself in for, and therefore you are making better risk decisions – formal risk assessment.
So why not apply this more formal risk assessment technique to important matters in your own life such as securing your home? It’s not really difficult, but you do have to know how to go about it. Here are the steps:
1. System characterization: For home security, the system you are considering is your house, its contents, the people who live there, the activities that take place there, etc. Although, you know these things intimately it never hurts to write them down. Something about viewing information on the written page helps clarify it in our minds.
-
Threat identification: In this step you imagine all the things that could threaten the security of your home and family. These would be such things as fire, bad weather, intruders, broken pipes, etc. For this (and other steps in the process), you can go beyond your own experience and see what threats other people have identified (i.e. google inquiries, insurance publications).
-
Vulnerability identification: This is where you pair up the threats you have just identified with weaknesses in your home and its use. For example, perhaps your house is located on low ground that is subject to flooding, or you live in a neighborhood where burglaries may occur, or you have old ungrounded electrical wiring that may short and cause a fire. These are all vulnerabilities.
-
Controls analysis: Controls analysis is simply listing the security mechanisms you already have in place. For example, security controls used around your home would be such things as locks on the doors and windows, alarm systems, motion-detecting lighting, etc.
-
Likelihood determination: In this step you decide how likely it is that the threat/vulnerability will actually occur. There are really two ways you can make this determination. One is to make your best guess based on knowledge and experience (qualitative judgement). The second is to do some research and calculation and try to come up with actual percentage numbers (quantitative judgement). For home purposes I definitely recommend qualitative judgement. You can simply rate the likelihood of occurrence as high, medium or low risk.
-
Impact analysis: In this step you decide what the consequences of threat/vulnerability realization will be. As with likelihood determination, this can be judged quantitatively or qualitatively, but for home purposes I recommend looking at worst-case scenarios. For example, if someone broke into your home, it could result in something as low impact as minor theft or vandalism, or it could result in very high impact such as serious injury or death. You should keep these more dire extremes in mind when you decide how you are going to treat the risks you find.
-
Risk determination: Risk is determined by factoring in how likely threat/vulnerability realizations is with the magnitude of the impact that could occur and the effectiveness of the controls you already have in place. For example you could rate the possibility of home invasion occurring as low, and the impact of the occurrence as high. This would make your initial risk rating a medium. Then you factor in the fact that you have an alarm system and un- pickable door locks in place, which would lower your final risk rating to low. That final rating is known as residual risk.
-
Risk treatment: That’s it! Once you have determined the level of residual risk, it is time to decide how to proceed from there. Is the risk of home invasion low enough that you think you don’t need to apply any other controls? That is called accepting risk. Is the risk high enough that you feel you need to add more security controls to bring it down? That is called risk limitation or remediation. Do you think that the overall risk of home invasion is just so great that you have to move away? That is called risk avoidance. Do you not want to treat the risk yourself at all, and so you get extra insurance and hire a security company? That is called risk transference.
So, next time you have to make a serious decision in your life such as changing jobs or buying a new house, why not apply the risk assessment process? It will allow you to make a more rational and informed decision, and you will have the comfort of knowing you did your best in making the decision.
Thanks to John Davis for this post.
Daily Log Monitoring and Increased Third Party Security Responsibilities: Here They Come!
For years now we at MSI have extoled the security benefits of daily log monitoring and reciprocal security practices between primary and third party entities present on computer networks. It is constantly being proven true that security incidents could be prevented, or at least quickly detected, if system logs were properly monitored and interpreted. It is also true that many serious information security incidents are the result of cyber criminals compromising third party service provider systems to gain indirect access to private networks.
I think that most large-network CISOs are well aware of these facts. So why aren’t these common security practices right now? The problem is that implementing effective log monitoring and third party security practices is plagued with difficulties. In fact, implementation has proven to be so difficult that organizations would rather suffer the security consequences than put these security controls in place. After all, it is cheaper and easier – usually – unless you are one of the companies that get pwned! Right now, organizations are gambling that they won’t be among the unfortunate – like Target. A fools’ paradise at best!
But there are higher concerns in play here than mere money and efficiency. What really is at stake is the privacy and security of all the system users – which one way or another means each and every one of us. None of us likes to know our private financial or medical or personal information has been exposed to public scrutiny or compromise, not to mention identity theft and ruined credit ratings. And what about utilities and manufacturing concerns? Failure to implement the best security measures among power concerns, for example, can easily lead to real disasters and even loss of human life. Which all means that it behooves us to implement controls like effective monitoring and vendor security management. There is no doubt about it. Sooner or later we are going to have to bite the bullet.
Unfortunately, private concerns are not going to change without prodding. That is where private and governmental regulatory bodies are going to come into play. They are going to have to force us to implement better information security. And it looks like one of the first steps in this process is being taken by the PCI Security Standards Council. Topics for their special interest group projects in 2015 are going to be daily log monitoring and shared security responsibilities for third party service providers.
That means that all those organizations out there that foster the use of or process credit cards are going to see new requirements in these fields in the next couple of years. Undoubtedly similar requirements for increased security measures will be seen in the governmental levels as well. So why wait until the last minute? If you start now implementing not only effective monitoring and 3rd party security, but other “best practices” security measures, it will be much less painful and more cost effective for you. You will also be helping us all by coming up with new ways to practically and effectively detect security incidents through system monitoring. How about increasing the use of low noise anomaly detectors such as honey pots? What about concentrating more on monitoring information leaving the network than what comes in? How about breaking massive networks into smaller parts that are easier monitor and secure? What ideas can you come up with to explore?
This post written by John Davis.
Tips for Writing Security Policy
Almost all organizations dread writing security policies. When I ask people why this process is so intimidating, the answer I get most often is that the task just seems overwhelming and they don’t know where to start. But this chore does not have to be as onerous or difficult as most people think. The key is pre-planning and taking one step at a time.
First you should outline all the policies you are going to need for your particular organization. Now this step itself is what I think intimidates people most. How are they supposed to ensure that they have all the policies they should have without going overboard and burdening the organization with too many and too restrictive policies? There are a few steps you can take to answer these questions:
- Examine existing information security policies used by other, similar organizations and open source information security policy templates such as those available at SANS. You can find these easily online. However, you should resist simply copying such policies and adopting them as your own. Just use them for ideas. Every organization is unique and security policies should always reflect the culture of the organization and be pertinent, usable and enforceable across the board.
- In reality, you should have information security policies for all of the business processes, facilities and equipment used by the organization. A good way to find out what these are is to look at the organizations business impact analysis (BIA). This most valuable of risk management studies will include all essential business processes and equipment needed to maintain business continuity. If the organization does not have a current BIA, you may have to interview personnel from all of the different business departments to get this information.
- If the organization is subject to information security or privacy regulation, such as financial institutions or health care concerns, you can easily download all of the information security policies mandated by these regulations and ensure that you include them in the organization’s security policy.
- You should also familiarize yourself with the available information security guidance such as ISO 27002, NIST 800-35, the Critical Security Controls for Effective Cyber Defense, etc. This guidance will give you a pool of available security controls that you can apply to fit your particular security needs and organizational culture.
Once you have the outline of your security needs in front of you it is time to start writing. You should begin with broad brush stroke, high level policies first and then add detail as you go along. Remember information security “policy” really includes policies, standards, guidelines and procedures. I’ve found it a very good idea to write “policy” in just that order.
Remember to constantly refer back to your outline and to consult with the business departments and users as you go along. It will take some adjustments and rewrites to make your policy complete and useable. Once you reach that stage, however, it is just a matter of keeping your policy current. Review and amend your security policy regularly to ensure it remains useable and enforceable. That way you won’t have to go through the whole process again!
This post by John Davis.
