Today, I just wanted to remind folks about the capabilities and use cases for HoneyPoint Security Server™. Got questions? Just ping us at info@microsolved.com.
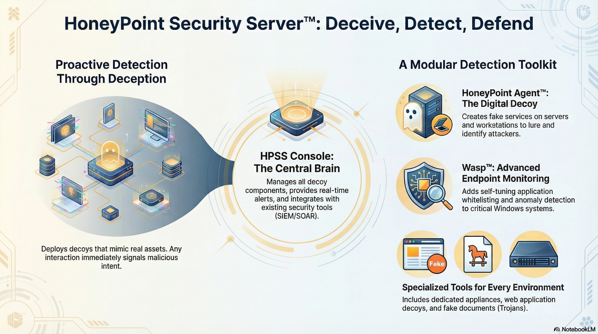

Today, I just wanted to remind folks about the capabilities and use cases for HoneyPoint Security Server™. Got questions? Just ping us at info@microsolved.com.
Today, managing vendor relationships has never been more critical. With increasing reliance on third-party vendors, organizations face heightened risks that can affect their operations and reputation. Vendor risk management (VRM) ensures that companies can identify, assess, and mitigate risks associated with their vendor partnerships, particularly as new challenges emerge. Traditional VRM methods often struggle to keep pace with the complexities of modern supply chains, which is where the application of artificial intelligence (AI) comes into play.
This article explores the various use cases for AI in vendor risk management, highlighting how it enhances risk assessment processes, addresses the limitations of conventional models, and discusses best practices for effectively implementing AI solutions.

In the intricate web of modern business, vendor risk management plays a pivotal role in safeguarding supply chain resilience and maintaining uninterrupted operations. With third-party relationships climbing in complexity and volume, the potential risks burgeon. Third-party risk management has therefore escalated to a critical business discipline.
AI-driven solutions transform how organizations evaluate and mitigate third-party risks. Real-time updates to vendor data, courtesy of Artificial Intelligence, diminish the dependence on stale reports, ensuring procurement teams wield current insights for informed decisions. Dynamic assessments of vendor performance and compliance, propelled by AI, augment abilities to pinpoint risks instantaneously.
Artificial Intelligence is revolutionizing Third-Party Risk Management by introducing efficiency, accuracy, and agility into the process. By automating the collection and analysis of risk data from various sources, AI not only enhances efficiency but also significantly improves the accuracy of the risk assessments.
A leading global bank implemented an AI-driven vendor risk management system to monitor its vast network of over 10,000 third-party vendors. The AI system continuously analyzes financial data, news feeds, and regulatory updates to provide real-time risk scores for each vendor. This implementation resulted in:
AI has a profound impact on the way organizations classify their vendors. Replacing once time-intensive manual tasks, AI systems process unstructured evidence and analyze vendor certification data at remarkable speeds. It can sift through thousands of vendor profiles, pinpoint the most relevant risks, and classify vendors according to their firmographics.
At the cornerstone of proactive risk management lies predictive analytics powered by AI. These models constantly monitor an array of factors, including market conditions, suppliers’ financial health, and geopolitical events, to foresee potential supply chain disruptions or vendor stability issues before they arise.
Traditional models of vendor risk management often encounter significant hurdles, particularly in the dynamic landscape of today’s cyber-threat environment. Here’s a comparison of traditional methods versus AI-driven approaches:
| Aspect | Traditional Method | AI-Driven Approach |
|---|---|---|
| Data Currency | Often relies on outdated information | Real-time data analysis and updates |
| Assessment Speed | Time-consuming manual processes | Rapid automated assessments |
| Risk Detection | Limited to known, historical risks | Predictive analytics for emerging risks |
| Scalability | Struggles with large vendor networks | Easily scales to manage thousands of vendors |
| Consistency | Prone to human error and bias | Consistent, data-driven assessments |
In the sphere of vendor risk management, integrating artificial intelligence (AI) can catalyze a transformation in managing and mitigating risks associated with third-party vendors. Best practices when implementing AI into such critical operations involve a holistic approach that spans dynamic risk assessments, automation of risk analysis, and enhancement of operational resilience.
A seamless integration of AI with existing supplier management systems ensures not only a cohesive workflow but also eases the adoption process for security teams. Organizations benefit from starting with a pilot program to gauge the impact of AI systems with real-world data before moving to a comprehensive deployment.
A successful AI integration in vendor risk management is contingent not just on technology itself, but also on the proficiency of the human intelligence behind it. Consequently, equipping the procurement team with essential skills and knowledge pertaining to AI technologies becomes paramount.
AI-powered tools have the potential to significantly bolster governance structures by enhancing transparency and offering traceable, auditable insights into business transactions and decision-making processes. By leveraging AI, organizations can actively maintain compliance with regulations, effectively mitigating risk exposure and promoting a culture of accountability.
While AI offers significant benefits in vendor risk management, it’s crucial to consider the ethical implications of its use:
Artificial intelligence has rapidly evolved from a novel innovation to a cornerstone of vendor risk management, and its trajectory points to even more sophisticated and strategic uses in the future.
Several breakthrough AI technologies are coming to the fore within vendor risk management paradigms:
The burgeoning use of AI in vendor risk management introduces intricate regulatory and compliance challenges. As organizations strive to comply with these myriad regulations, a shift is necessary from a static assessment model to continuous, internal governance that actively keeps pace with regulatory evolution.
AI-driven vendor risk management represents a significant leap forward in how organizations approach third-party risks. By leveraging advanced technologies like machine learning, natural language processing, and predictive analytics, businesses can achieve more accurate, efficient, and proactive risk management strategies. As AI continues to evolve, it will undoubtedly play an increasingly crucial role in safeguarding supply chains, ensuring compliance, and driving strategic decision-making in vendor relationships.
However, the successful implementation of AI in vendor risk management requires careful planning, continuous learning, and a commitment to ethical practices. Organizations must balance the power of AI with human oversight and judgment to create a robust, effective, and responsible vendor risk management framework.
Ready to harness the power of AI for your vendor risk management? MicroSolved, Inc. is at the forefront of AI-driven security solutions, offering cutting-edge tools and expertise to help organizations like yours transform their approach to vendor risk.
Our team of experts can help you:
Don’t let vendor risks compromise your business. Contact MicroSolved, Inc. (info@microsolved.com) today for a free consultation and discover how AI can revolutionize your vendor risk management strategy.
* AI tools were used as a research assistant for this content.
Lately, I have been working on using the Cynefin framework to help a client with supply chain risk management. I’m not going to dig into the specifics here, but I wanted to share a quick workflow that we used during this process that has been very useful for us.
First, we built a risk matrix for supply chain risk. Basically, there are a number of these available via the various search engines. We took some of the most common ones and tore them down to commonalities, then built them into our matrix. We turned this into a simple spreadsheet.
Next, once we had our risk matrix, we did an exercise where we heat mapped the various risks, scoring them high/medium/low subjectively. This gave us an excellent tool to monitor our situation and communicate it with our stakeholders.
Next, we mapped all of the high risks into the cynefin framework by researching the present state of each, whether best practices were available and relevant, being developed, or still in the experimental stage. This gave us a good idea of which problems we could simply focus on using known techniques and skills against, which ones we needed to take existing decent practices and optimize them, and which problems we needed to experiment with solutions for.
Overall, the exercise took around an hour to complete once we compiled the basic templates and completed the risk matrix research. For those of you facing complex risk management problems, this workflow might assist. Let me know on social media (@lbhuston) if it provides any help or if you have suggestions and feedback. Thanks for reading!
I wanted to share a recent success story from our TigerTrax work with you. The TigerTrax platform is opening a wide-variety of new opportunities for MSI. We are building entirely new suites of services around the platform and the unique capabilities it provides for us.
Recently, we were asked by a client to use TigerTrax to perform investigations on a foreign bank run attack that occurred a few months ago. The client wanted to use the research to fully understand how the attack was performed, what mechanisms were used to influence the public decisions to cause the bank run and to identify the possible motives of the attackers involved.
The MSI Intelligence Team, now staffed with 3 full time dedicated analysts, deconstructed the events and used a variety of analytics to investigate the attacks. The team identified a variety of possible motives, ranked them by probability and provided them to the client. They also built a step by step time line of the attack details, provided sample social media and traditional media examples, wrote a detailed scenario testing process for the client to use to test their own financial management mechanisms against the threats and briefed the client on their findings.
The client was amazed at how quickly, concisely and clearly the data was analyzed. The Intelligence Team rose past their expectations and gave them actionable intelligence that they could use to not only better understand the attack, but also test their exposures to such an attack in the future!
The success stories around TigerTrax are continuing to pile up, and I look forward to sharing more of them in the near future. In the coming months, you will hear even more about our new spin-off company, called The Bodhi Foundry, which we have built to hold all of the non-security products that the TigerTrax platform is powering. That company is focusing in on branding intelligence, competitive analysis, product innovation research and a wide variety of specialized business data analytics. But, never fear, the core use care of TigerTrax remains information security, threat intelligence, studying cyber-crime and helping our clients use data analytics in new ways to solve old-school security problems.
As always, thanks for reading and until next time, stay safe out there!
Recently, I have been spending a lot of my time working with TigerTrax, our intelligence platform, and using it to further my research into emerging threats. One of the most interesting areas has been using to track and trace the fits and starts of malware evolution using social media data and the web.
TigerTrax is really good at finding and analyzing the data for trends. The visualizations make spotting emerging patterns and even outliers very easy. For example, we noticed a trend around side loading of malware payloads recently. Not an overwhelming trend across all of malware, but associated with a specific group of verticals being targeted. This emerged easily from the graph data and analytics engines. We were able to use that information to inform our customers in that space and increase their capabilities in detection and incident response.
We have only just begun to find the deeper use cases for TigerTrax, but it is already changing the way MSI does work, even the core work of assessments. For example, with a small window of lead time, we can generate specific pattern analysis and cases to support findings in risk assessments, vulnerability and pen-testing work. The engines can keep our scenarios refreshed, keep us up to date with the latest attack vectors and exploits being used in the wild.
All in all, TigerTrax has given us a larger view of infosec, and watching malware evolve through its lens has become an interesting part of what we do at MSI. We look forward to the day when we can discuss more publicly what we are doing with TigerTrax and some of the findings we are generating, but for now, just know that the platform is being used in a myriad of ways, and that new developments are occurring on a daily basis. If you’d like to discuss what TigerTrax can do for your organization, give us a call. We’d be happy to sit down for a briefing with your team.
Recently, my team was asked to use our TigerTrax platform to observe a body of social media content around a specific topic for 12 hours and extract meaningful data. The topic chosen by the client was “fracking”.
As you might expect, there was quite a bit of conversation on the Internet about fracking during that period. The client wanted specifically to focus on a specific set of data and to identify potential activism or criminal activities that might be gathered from the data set. So, mission in hand, we engaged the TigerTrax platform and after 12 hours of data gathering, began our analysis.
The data we extracted was pretty amazing to the client. They were quite interested in some of the findings. For example, we identified and presented the client with:
The client was able to use this information to help educate their membership, strengthen their security during protest events and to better understand some of the emerging PR concerns around their operations. They also began to work with ISPs and other service providers to begin takedown requests for the more illicit content.
This is just a sample of some of the ways that clients are leveraging the new TigerTrax platform to assist them with business needs. Get in touch and let us know your ideas or specific problems and we will see how we can help. If you want to know what the world is saying and how it affects you, TigerTrax just might be the solution you are looking for.
Topic analysis can be performed with TigerTrax as a single deep dive event with a customized report delivered and open for re-use with other clients, or can be completely customized to the client organization and solely for their use. Ongoing monitoring and analysis of topics and events can also be done as a part of the TigerTrax services. If you would like to hear more about the TigerTrax platform, or Topic Analysis, please give us a call at (614) 351-1237 extension 206. You can also reach out to me on Twitter (@lbhuston), and we can arrange a discussion.
As always, thanks for reading and until next time, stay safe out there.

By now, you may have heard about our new TigerTrax™ powered services. We formally announced them this week and the interest in them has been very high. Today, I wanted to provide a bit more context to the last year or so, especially around a particular use case for TigerTrax that is pretty unique and intriguing.
We originally developed the TigerTrax platform to super charge our threat intelligence activities against real bad guys in the world. It grew out of our need to better manage and explore the vast amounts of data we get from the HoneyPoint Internet Threat Monitoring Environment (HITME), but even as we leveraged it against cyber-crime, other use cases quickly emerged.
One of these use cases was developed by engaging directly with an NFL team. The team worked with us over a number of months as we tweaked out the capabilities of the system and adapted it to more of a social focus than a crime focus for their needs. Today, the system provides ongoing monitoring of a number of social media sites and their content, continually providing for both positive examples of expected behavior, as well as identifying violations of the player code of conduct. With all of the press and public media attention to some high profile examples of athlete misconduct, the teams are now taking this very seriously.
MSI has developed TigerTrax into a modular platform that easily scales to monitoring all of the player, cheerleader, coaching, back-office and ownership staff against the code of conduct. The social media content is gathered in near real time, and an analytics engine provides advanced techniques to flagging potential behavioral issues. The system is also continually adapted to new forms of behavior, shifting social issues (bullying, homophobic and racial issues, etc.) and the evolving concerns of the team management. Combining the TigerTrax technology with a team of deeply skilled human analysts, strong player skill development expertise and social media education focused on personal branding and social leadership was a natural fit for the evangelical approaches that MSI has practiced for more than 20 years in our information security engagements.
In addition, one of the key differentiators of TigerTrax, is not just the analysis of the key parties’ (players, cheerleaders, coaches, etc.) content, but also the global content from the social media sphere around specific events and actors. Using this crowd-sourced sensor approach, we have been able to identify misbehaviors and code of conduct violations, simply by capturing the data and correlating/validating it from observers in the public. The same techniques have also allowed us to use the public data to defend players and other parties against grossly exaggerated or completely false accusations against their character. Indeed, for some players, TigerTrax has made an excellent tool in DEFENDING their reputations!
Over the last few years, we have taken the initial platform developed for threat intelligence against cyber-crime, and adapted it to a variety of professional sports, business applications, investigative and forensic activities. We have expanded the platform beyond simple keyword analytics and are beginning to actuate on sentiment, data flow anomalies and deeper content analytical problem solving. In the years to come, we view TigerTrax as a very capable core business empowerment platform for MSI, just as impactful as HoneyPoint has been since 2006. We are still developing use cases for TigerTrax and the service offerings it has empowered for our clients. If you have a potential new use case that you would like to discuss, or if you would like to hear more about reputational threat intelligence and monitoring, please give us a call.
MSI is also seeking a handful of key business partners interested in helping us grow the TigerTrax platform adoption by bringing these unique capabilities to their clients, or by adapting the capabilities into new service offerings. If your business has an idea for how to leverage the TigerTrax capabilities, give us a call. We will be happy to explore new solutions with you.
As always, thanks for reading and thanks for partnering with MSI!
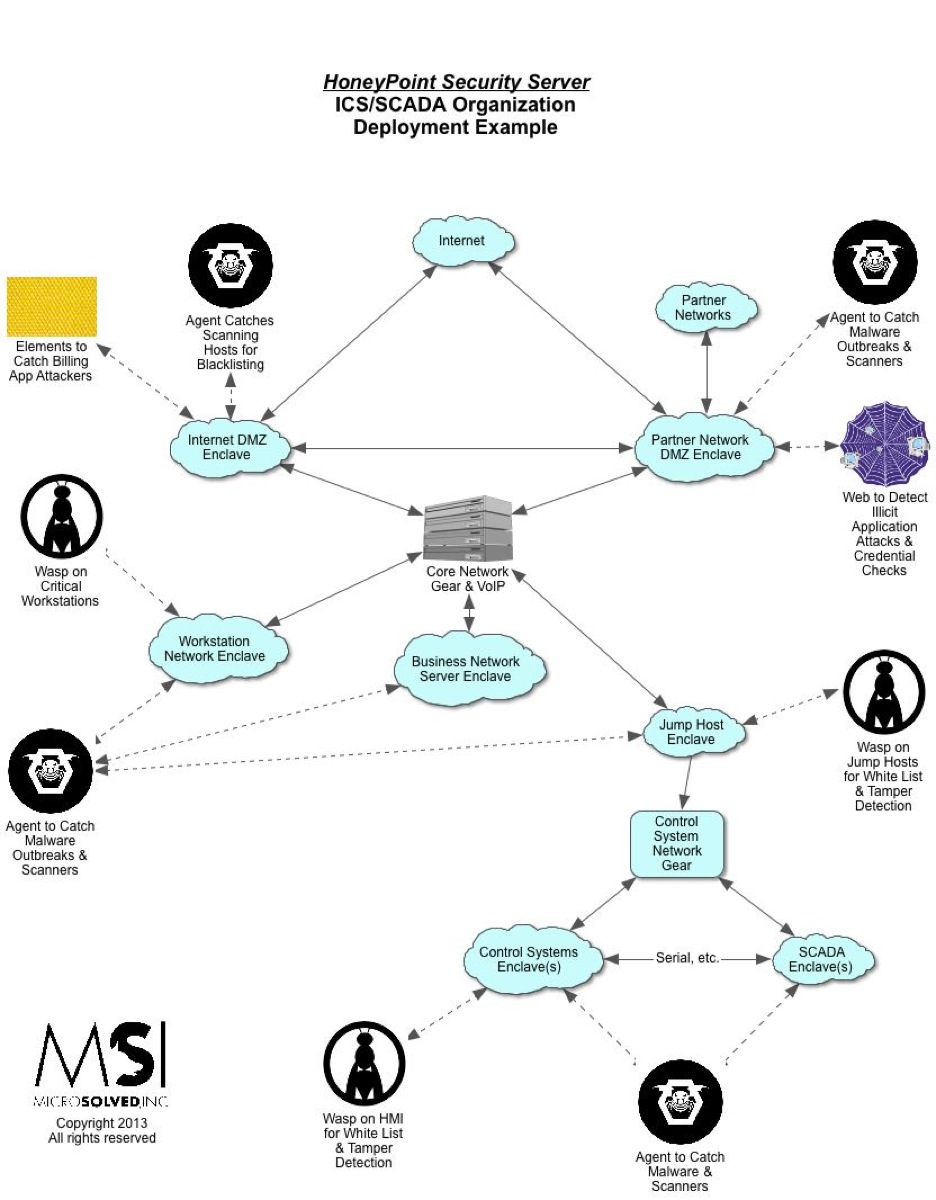
Recently, there have been several questions about potential deployment scenarios for HoneyPoint Security Server in and around ICS and SCADA organizations. Here is a quick, high level view of what a sample deployment might look like in a utility or other ICS environment. Note that the sample environment has fully embraced enclaveing. The network is fully segmented based on function.
In organizations where segmentation or the use of enclaves has not been established, HPSS can still be used and would be deployed in much the same manner.
Please let us know if you have any questions about this diagram or about deploying HPSS in your environment. We would be happy to set up a free consultation with you to discuss how the tool could aid in your detection program and give you increased visibility throughout your enterprise.
PS – If the graphic is difficult to read, right click on it and select view in new tab. The theme for the site is having trouble with this particular graphic.